If you’ve ever received a fake email from one of your “executives” asking for a quick request, you’re not alone. In fact, new research from the Agari Cyber Intelligence Division shows that individual impersonation attempts now comprise nearly a quarter of all BEC attacks. This is an increase from the last quarter, when this type of scam made up only 12% of all attacks.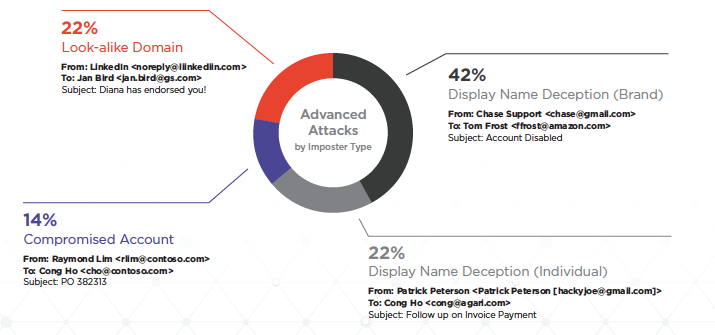
Gift Cards Remain On Top
What do these fake executives want? Most are asking for gift cards, a trend we expect to continue as the holiday season approaches. Over the past quarter, BEC scammers requested 20 different types of gift cards. But cards belonging to five brands—Google Play, Steam Wallet, Amazon, Walmart, and eBay—continued to rank among the most dominant, figuring into nearly three in every four requests.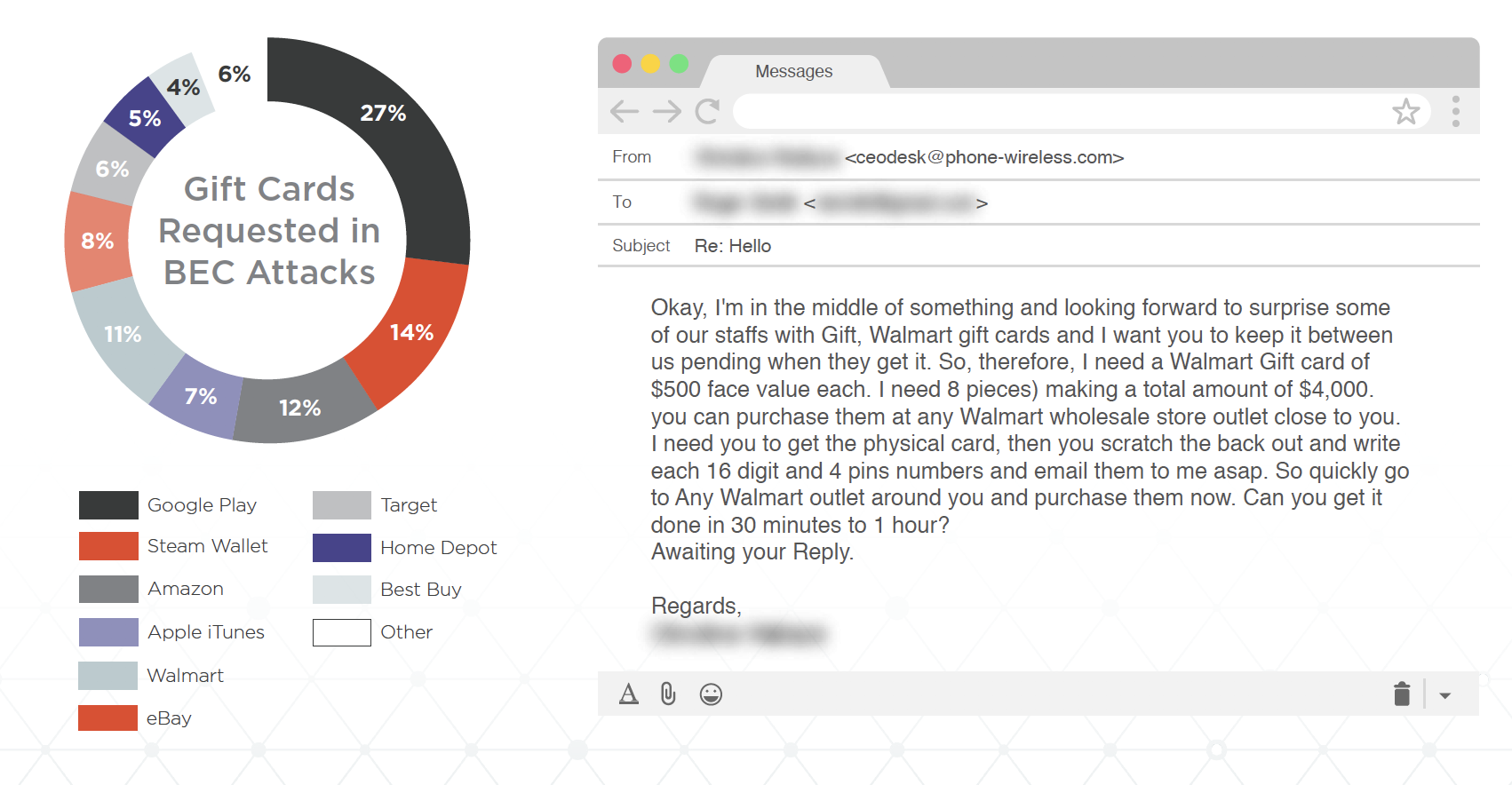
That said, a fair number are also asking for payroll diversion, a tactic used to deposit the paycheck of an employee (typically a well-paid executive) straight into an account controlled by the cybercriminals. These cons primarily target employees in Human Resources with emails designed to trick them into changing the direct deposit details for an employee or executive to a bank account controlled by the fraudster.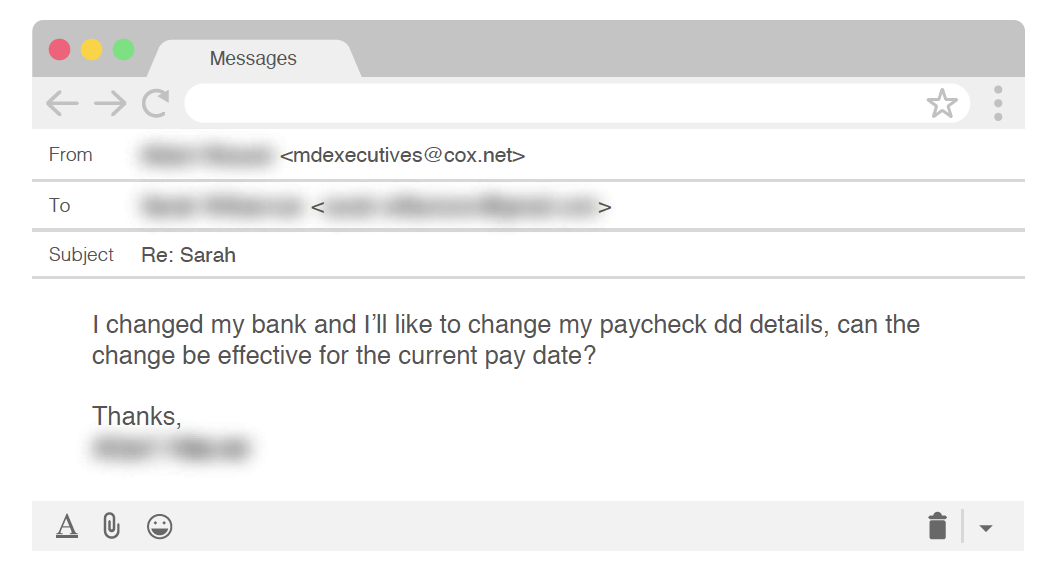
The other attack type of choice is the typical wire transfer request, which perhaps experienced a drop as more employees become aware of this type of scam.
Money Talks, But Volume Talks More
Perhaps most interesting is the amount of money requested in these scams. During the past quarter, the average dollar amount for gift cards requested in BEC scams was just over $1,500, compared to more than $52,000 for attacks leveraging wire transfers. This disparity has made gift card-based BEC scams a numbers game propelled by volume and attack cadence.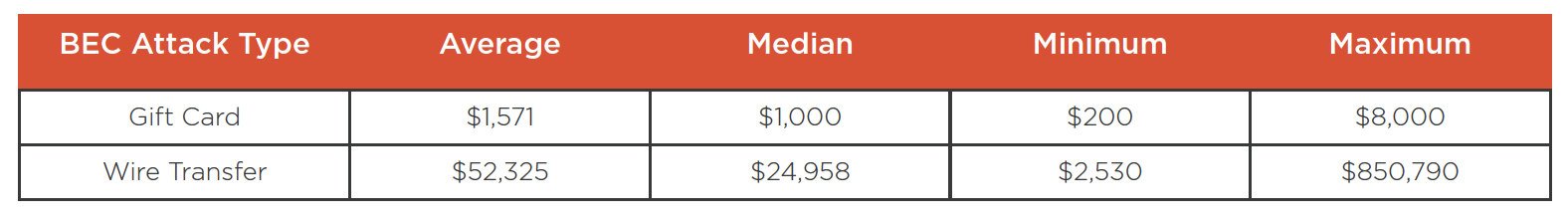
Still, the modest rise in wire transfer attacks may be cause for concern. According to the U.S. Treasury Department, businesses lose as much as $300 million a month to BEC scams in all its forms. But half of those losses are attributed to con artists seeking wire transfers on fraudulent payments. In our report on the cybercriminal group Silent Starling, we look at a troubling new BEC trend that we call vendor email compromise (VEC), in which fraudsters use compromised employee email accounts to target not just one company, but entire supply chain ecosystems.
BEC Continues to Grow
All this to say... business email compromise scams aren’t going away anytime soon. But they are becoming harder to spot. Our best advice for staying safe this holiday season?
- Triple-check the header information in your emails, especially those that include requests coming from executives or people in authority.
- If you can’t verify that the request is legitimate over email, reach out via another form of communication. This extra step only takes a few minutes, and it could save your organization thousands in dollars lost.
- Forward emails to your executives rather than replying directly. By forwarding the email, the correct email address has to be manually selected, ensuring that a tricky look-alike domain doesn’t enable cybercriminals to take advantage of you.
There is little denying that business email compromise is big business. Until organizations take proactive measures to stop these emails from reaching the inbox, we must all be aware—or else the eye-popping revenues cybercriminals generate with so little effort will continue to increase, one gift card at a time.
Learn more about our recent BEC research in the Q4 2019 Email Fraud and Identity Deception Trends report.