Every year, the Internet Crime Complaint Center, also known as IC3, publishes an annual report looking at the different types of internet-based crimes reported to the FBI. Over the last year, victims around the globe lost $2.71 billion to all types of cybercrime, which includes lottery scams, hacktivism, gambling fraud, malware, ransomware attacks, and tech support fraud, among others. While each of these is an issue within itself, Agari is focused on researching and stopping the types of attacks that hit enterprises—namely business email compromise, spear phishing, and consumer phishing.
Business Email Compromise Continues to Rise
When IC3 first considered business email compromise as its own category in 2015, the number reported was $246 million—the highest of any category in dollars lost, but seventeenth on the list in total victims, showing just how profitable this type of crime is. The next year, IC3 reported a total loss of $360 million for BEC crime and the following year in 2017, that total nearly doubled to $675 million. Last year, that number nearly doubled yet again to almost $1.3 billion in losses, with the category rising to sixth on the list by total victim count.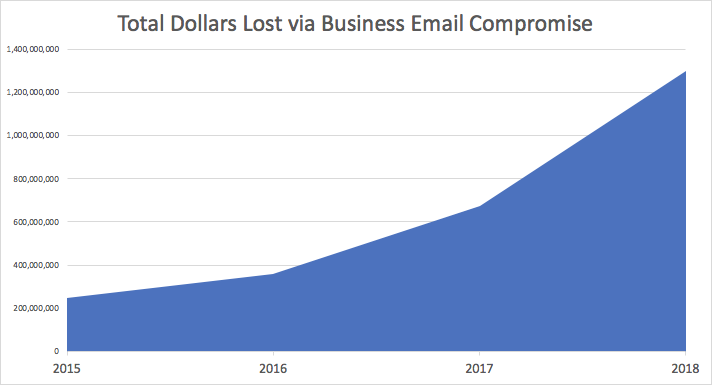
Why is business email compromise as a category continuing to double year over year? With more organizations building awareness amongst their employees and implementing solutions like Cloud Email Protection to fight BEC, we would think that this should start to decline after some time.
Unfortunately, BEC is big business for cybercriminals, and we’re seeing it continue to expand likely because it is easy. With a simple (and oftentimes free) lead generation service, these cybergangs can find thousands of targets and send a one-sentence email from the company CEO or high-level executive asking for their attention to a particular issue. Since employees are eager to please their boss with a timely response, they often complete the wire transfer request or send the requested information without ever verifying that the person they're communicating with is actually who they say they are. Combined with the fact that many people are working from their mobile phones, which typically display only the sender’s name, cybercriminals are learning how to quickly and easily exploit their victims.
Another fact that makes business email compromise cases easier to pull off—and something that impacts how believable these scams are—is that BEC is often tied to romance scams. Our research has shown that many people who are involved in online relationships with these criminals are doing their part to defraud big business, typically by laundering the money through a US-based bank account they have set up to “help” their online soulmate. By taking this into consideration, we can see how interrelated and prevalent these crimes are.
BEC Coincides with Other Types of Crime
When we start crunching the numbers in the report, the total losses in 2018, including social media and virtual currency fraud, tops out at $3.7 billion—with BEC and romance scams leading the pack at 44.9% of all losses reported to IC3.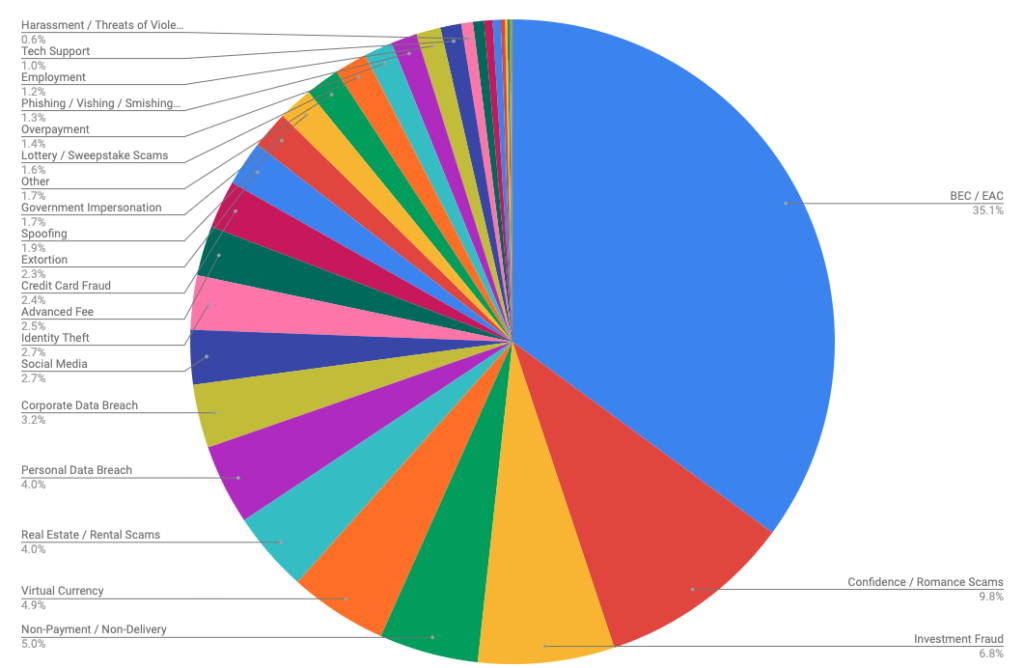
As mentioned above, our research has found that much of this is likely related. For instance, we have identified BEC actors taking part in other types of listed crimes such as identity theft, carding, spoofing, lottery scams, overpayment fraud, phishing, and employment fraud, just to name a few. In a recent report, we found that a group we’ve named Scarlet Widow has continued with multiple methods of fraud—starting in Craigslist scam and real estate fraud, then transitioning to wildly successful romance scams, which they continue alongside their more profitable BEC fraud today.
In another instance, a group we've named London Blue started with Craiglist scams and credential phishing, before then turning over to the big business of BEC. While they now focus almost entirely on business email compromise scams around the world, they were still continuing with other various types of crime until recently. All this to say that what the IC3 report breaks out in the categories above is likely not as disparate as we would believe.
What to Expect When You’re Expecting a BEC Scam
We’re nearly halfway through 2019, and cybercrime is, unfortunately, more profitable than ever. As we think about predictions for the next Internet Crime Report, we have to keep a few things in mind.
With the increase in knowledge around business email compromise, more people are talking about this very effective type of fraud than ever before. All equal, we would expect to see business email compromise success take a nosedive as more organizations install the measures needed to protect their employees. That said, the people behind these scams are smart—they’re using translation tools to make their emails sound more believable and legitimate lead generation services to find new targets, ensuring that there is always someone to be fooled by a fake email. The people behind BEC are resourceful and will do anything they can to make a dollar—a fact that will contribute to more cybercrime in the coming year.
So what are our predictions for 2019? Unless organizations around the globe allocate the resources and training needed to fight business email compromise, we will be in the same position in 2020. Based on growth patterns form 2015 to 2018, we expect that we’ll reach that $2 billion number in the 2019 Internet Crime Report—and that may be a conservative guess. We hope we are wrong, but only time will tell.