Historically, business email compromise (BEC) threat actors have used wire transfers as a means to steal money from businesses. Impersonating a trusted contact, usually a company executive, a scammer requests that a fictitious vendor get paid by sending money to a bank account controlled by the scammer or an associate. Today though, we've seen a new trend: cybercriminals outright asking for bitcoin.
Over the past year, the cash out methods used by these scammers have started to evolve. Instead of using vendor payments as a con, some BEC attacks have shifted to diverting payroll direct deposits. Even more recently, scammers have moved away from bank accounts as a mechanism to receive their illicit funds as gift cards have become a burgeoning cash out method—likely because they are less reversible, more anonymous, and do not require the need for a middleman. In our recent report on a BEC group called Scarlet Widow, we detailed how West African cybercrime groups launder stolen gift cards through online cryptocurrency exchanges.
But like death and taxes, it’s a certainty that scammers will continue to develop new ways to steal money from their victims. During a recent engagement with a scammer, we observed a potential next step in BEC financial exfiltration: bitcoin itself.
Bitcoin offers the same advantages as gift cards—anonymity, irreversibility, and lack of need for a financial intermediary—so it was only a matter of time before BEC scammers stuck their toe into the water to see if cryptocurrency is a viable cash-out mechanism.
Last week, using a persona we created and posing as a financial executive, we initiated an engagement with a BEC actor who was looking to get a payment sent to a fictitious vendor. The exchange started with the same pattern that we see in many of our engagements: the scammer requests that a wire transfer be made to a supposed vendor bank account, the transaction “fails” for a variety of reasons, and the scammer sends another mule account to attempt the transfer again.
After a few failed wire transfers (and undoubtedly, growing frustration), the scammer sent over a third mule account. This time, however, he mentioned that he could also provide a “Bitcoin account number” that could be used to pay the fake vendor.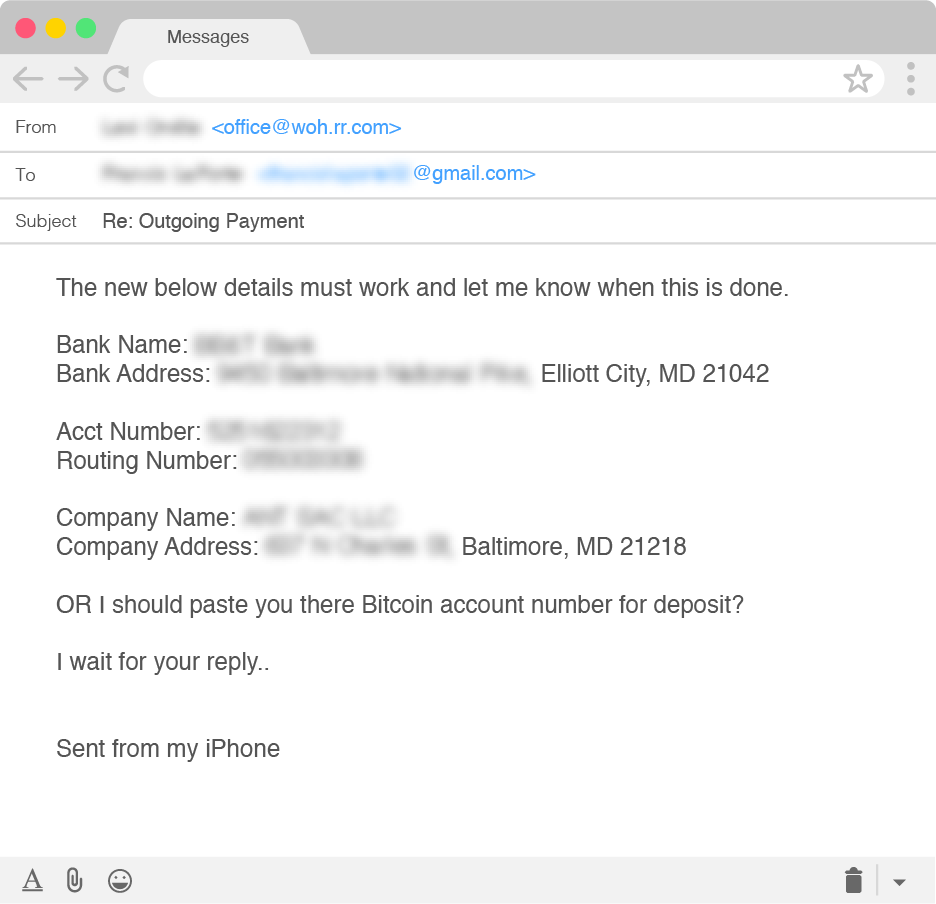
This was the first time we’ve observed a scammer offer the possibility of using a bitcoin wallet to receive funds from a BEC scam. Consider our interest officially piqued!
At this point, we changed our engagement tactics from obtaining additional mule bank accounts to focusing on the scammer’s bitcoin accounts.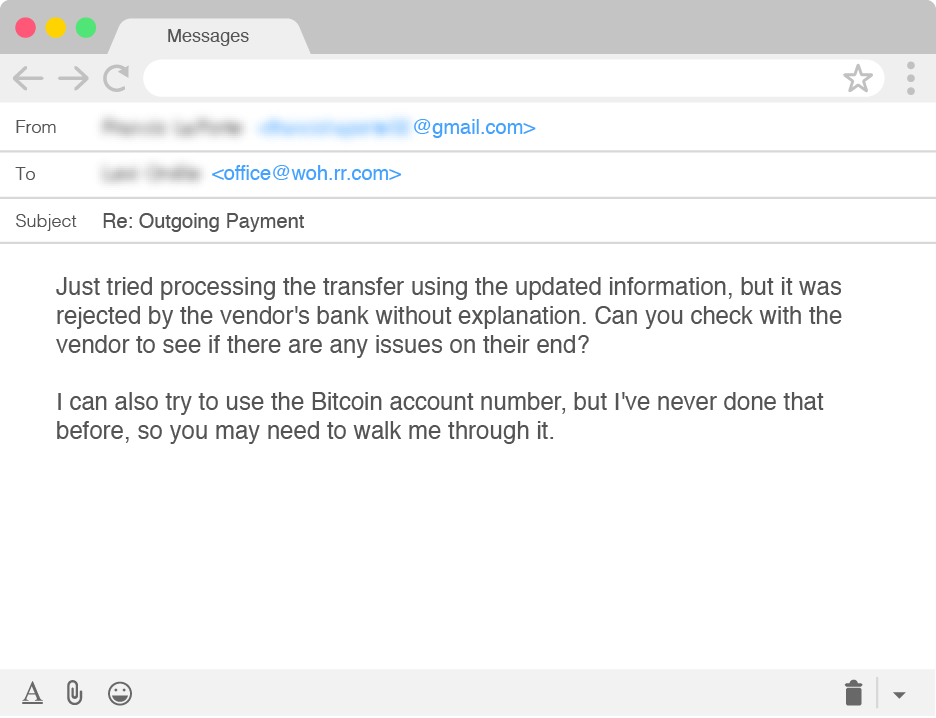
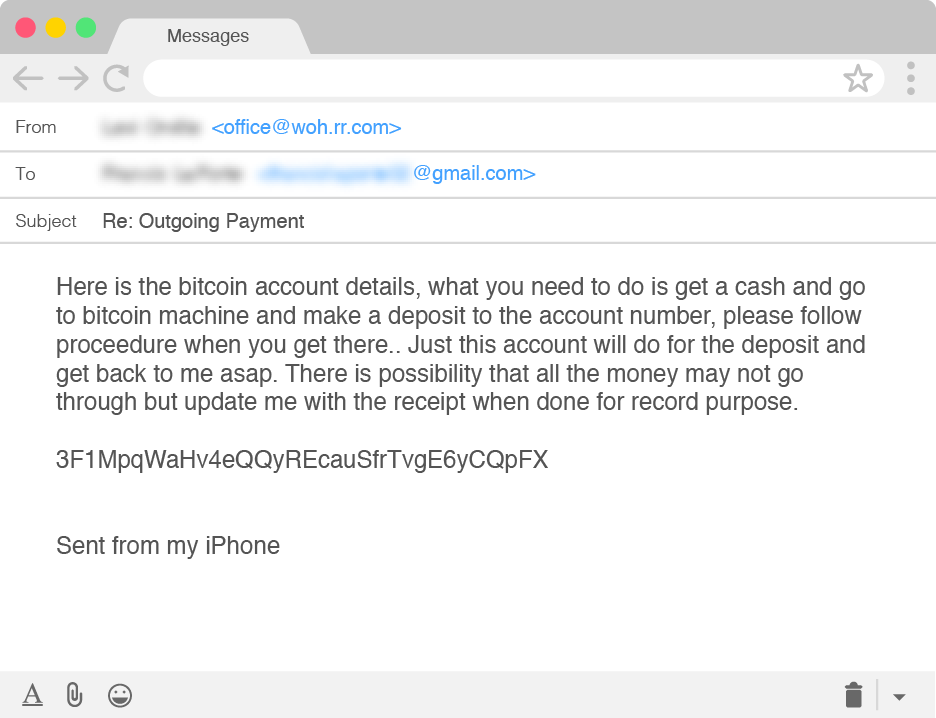
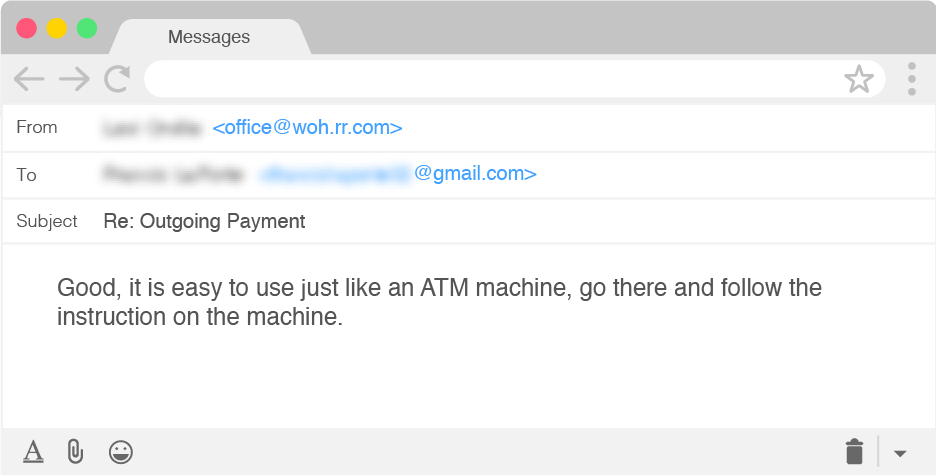
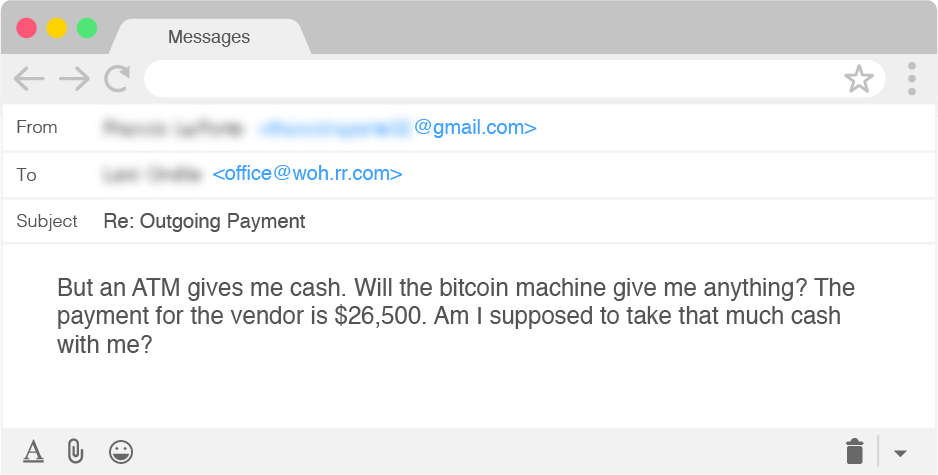
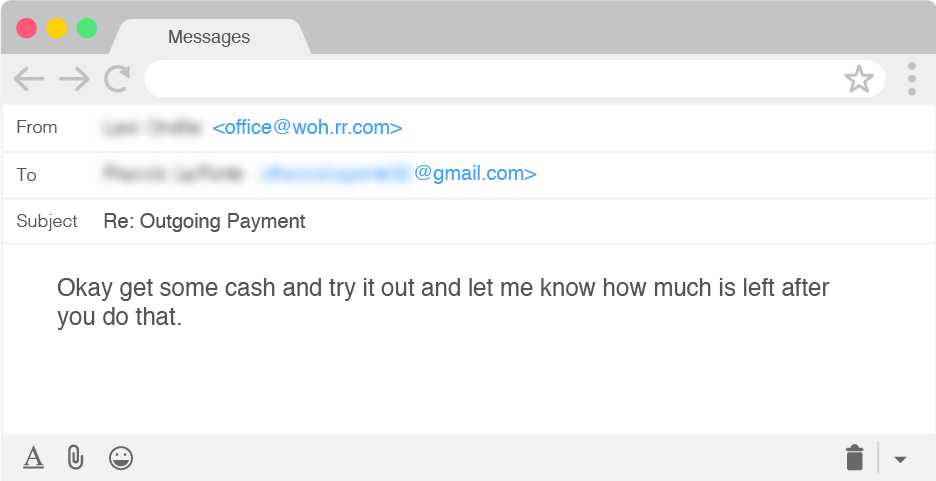
The bitcoin address provided by the scammer currently has no previous transactions associated with it. The request from the scammer to find a physical bitcoin machine caught our attention, as that is an extremely inconvenient and inefficient way to continue with the transaction as opposed to asking us to create a wallet and transfer funds online, similar to instructions provided in ransomware attacks. Continuing our engagement, we played coy with the scammer to try to understand just how much he knows about the intricacies of cryptocurrency transactions. The engagement continued as follows: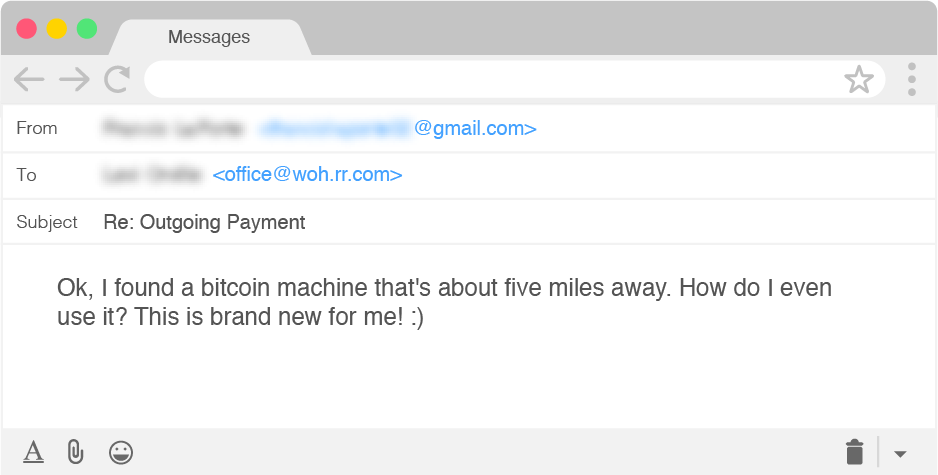
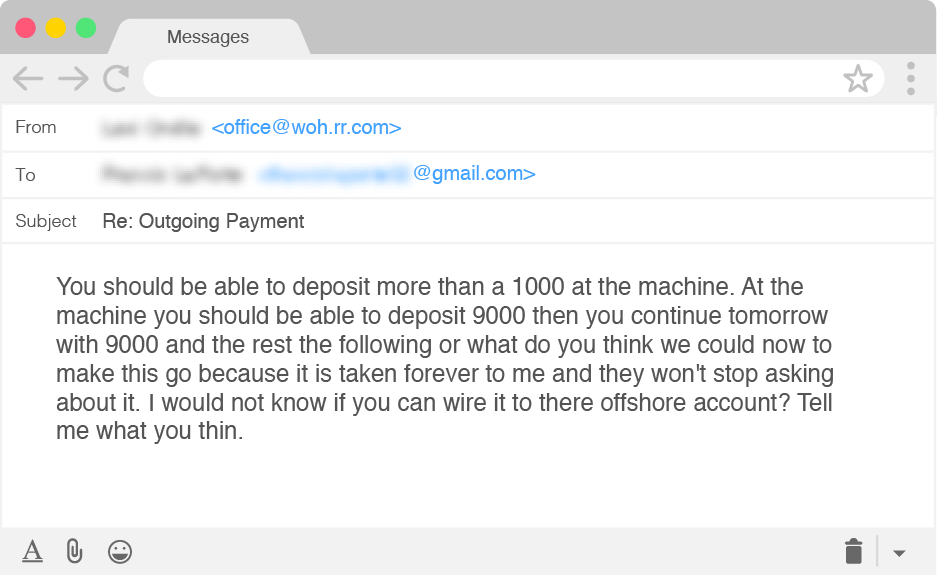
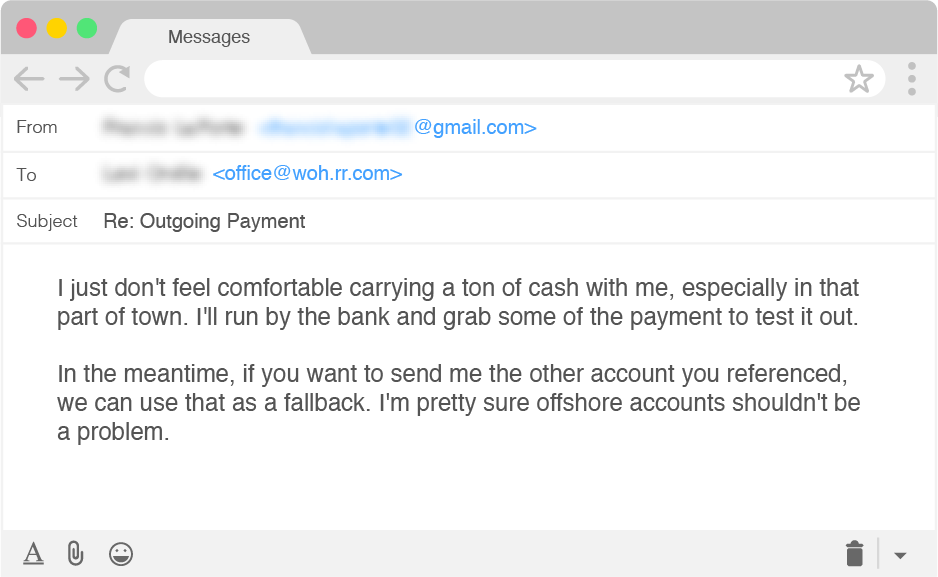
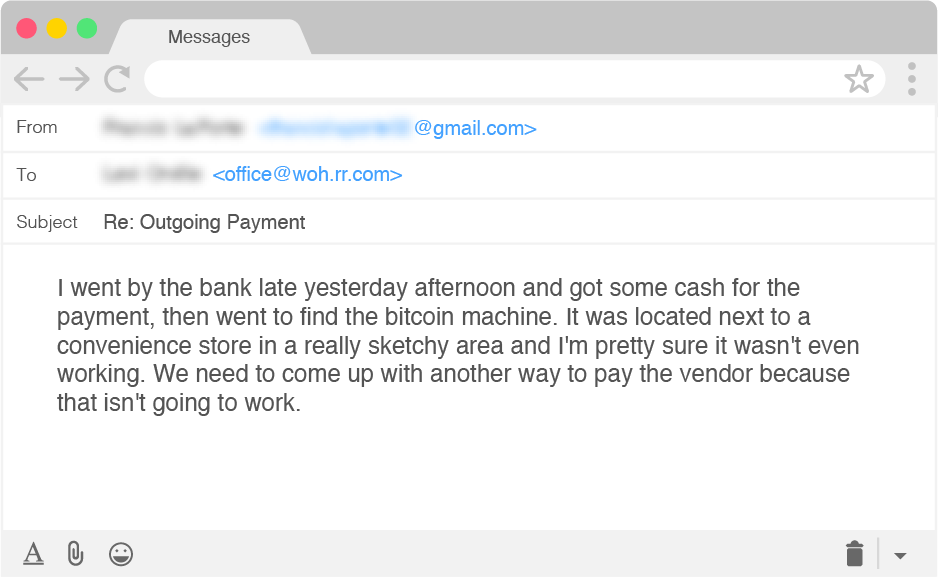
At this point, the scammer gave up trying to teach us how to properly use a bitcoin ATM and moved on to asking us to send physical checks to an address in Maine. This, of course, still failed miserably.
What this engagement tells us is that while scammers may not be experts at cryptocurrency transactions, they are testing the viability of using bitcoin as a medium to transfer illicit funds. Based on data from the recently released 2018 FBI Internet Crime Report, the number of reported cybercrime incidents associated with virtual currencies increased by 780 percent between 2017 and 2018.
Much of this increase is likely attributed to the significant increase in cyber extortion incidents, but as cybercriminals evolve and learn from one another, we should expect scammers involved in other types of fraud to follow suit in due course. If BEC scammers end up jumping on the bitcoin bandwagon, we can expect the number of cryptocurrency-related fraud cases to continue to rise dramatically in 2019.
Learn more about how cybercriminals are using bitcoin in our recent report on the group we've named Scarlet Widow.
Bitcoin: The Next Evolution in BEC Cash Out Methods?
Posted on April 25, 2019