Here’s some earned media you don’t want for your brand—headlines announcing that your customers are victims of a “nasty phishing scam” or that your “accounts are under attack.” Verizon and Microsoft have had to manage those headlines in recent months. And other tech companies are vulnerable to the same kind of brand damage right now. That’s because organized cybercriminals are going all-in on brand impersonation scams, and many tech brands have yet to shore up their email security.
Going After Brands in Impersonation Attempts
In April, Verizon customers reported getting “customer support” emails that directed them to fake but convincing looking sites to enter their account information for a “discount.” The sites they were directed to asked for their phone numbers, PINs, passwords, and knowledge-based authentication details like the name of the customer’s first roommate. Now, customers who took the bait are at risk for identity theft and mobile account takeover.
Microsoft, meanwhile, has to contend with a growing number of cybercriminals using the Microsoft domain to send brand impersonation scams, with multiple entities involved. In addition to using Microsoft, criminals also use domains for OneDrive and LinkedIn—both part of the Microsoft ecosystem. Other common technology companies seeing an increase in impersonation include Facebook and Netflix.
Stolen Data, Broken Trust
Unfortunately for brands, these crimes steal more than victims’ information and money. They also erode the trust that technology companies like Microsoft and Verizon spend so much time and money building with their customers, vendors, and partners. That trust is exactly why cybercriminals target those businesses—and part of the reason Microsoft tops the list of most-impersonated brands.
When people lose trust in your brand, either because they were victims of scammers impersonating your company or because they read about a scam leveraging your brand name, they’re less likely to open your emails. That drags down the ROI on your demand generation campaigns and makes it hard to keep those relationships alive. The worst part is that most advanced email attacks that impersonate trusted brands can be prevented with technology that already exists.
Tech Lags in DMARC Implementation
It’s clear that email-based brand impersonation attacks are on the increase because cybercriminals are getting better at running complex scams. What is not always obvious is that solutions to the problem already exist. And many tech companies haven’t adopted them yet.
The first is DMARC, an open standard for email sender authentication that shows you who is using your email domains. It lets you stop unauthorized email from your legitimate domains from reaching recipients’ inboxes. And it proves that legitimate email is authenticated, giving recipients extra verification that they can trust the email.
Despite its power to stop domain-based phishing attacks, DMARC adoption has been slow. When our research team looked at the 328 million global domains configured to send email, there were only seven million domains with DMARC records—a mere 2% of all domains worldwide.
The low rate of DMARC implementation may be understandable for organizations outside the tech industry, where email security risks may not be top of mind for decision-makers. But what is surprising is the low DMARC adoption and enforcement rates among large tech companies.
When the Agari Cyber Intelligence Division looked at DNS records for domains belonging to $1 billion-and-up tech companies over the last quarter, we found that 40% had no published DMARC record at all. And only 8% had implemented full enforcement with a p=reject policy to keep unauthorized emails from reaching their targets.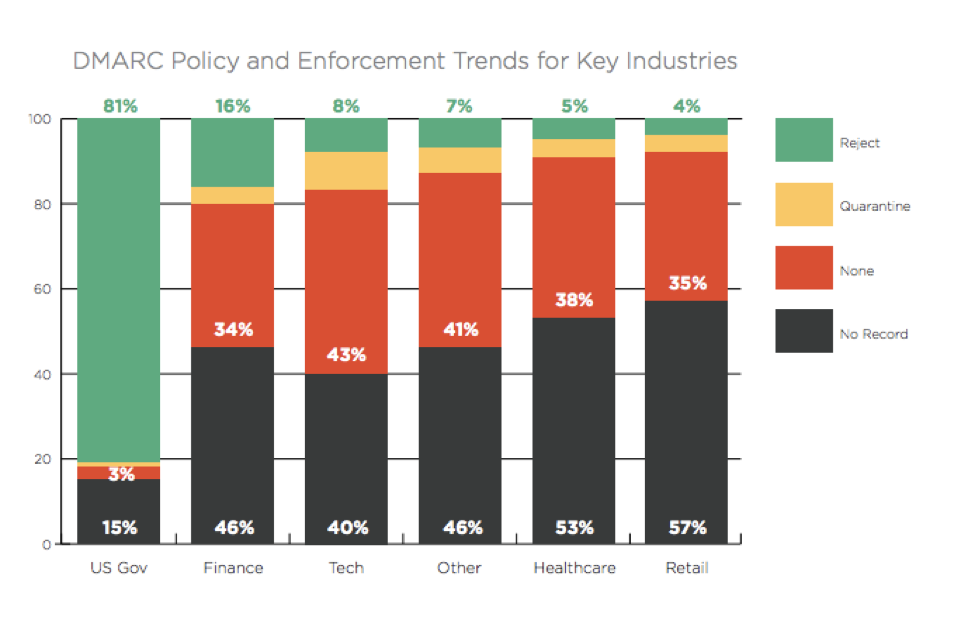
Tech companies are on the leading edge in so many ways. It’s time to add email authentication to the mix. Keep criminals from impersonating your company via email, and keep your brand out of negative headlines, so your customers can continue to trust the emails you send them. If you don't, the results could be catastrophic.
See if your technology company is included in the 8% of domains with a p=reject policy with our Look Up or Generate a DMARC Record tool.