Recently, news broke about how a sophisticated Nigerian cybercriminal organization has been committing mass unemployment fraud against a number of states, including Florida, Massachusetts, North Carolina, Oklahoma, Rhode Island, Washington, and Wyoming. Based on information uncovered by the Agari Cyber Intelligence Division, some, if not all, the actors behind these fraudulent schemes are likely part of Scattered Canary, a Nigerian cybercrime group about which we released a detailed report last June. As we detailed last year, Scattered Canary has been involved in a wide variety of fraudulent activity against government services over their 10+ year history, including unemployment fraud, social security fraud, disaster relief fraud, and student aid fraud.
In addition to the fraudulent unemployment activity against these states, we have also found evidence that links Scattered Canary to previous attacks targeting CARES Act Economic Impact Payments, which were meant to provide relief caused by the COVID-19 pandemic, as well as new scams targeting Hawaii unemployment benefits. We have also identified the methods Scattered Canary is using to create numerous accounts on government websites and where the stolen funds are directed.
Scaling Operations with Google Dot Accounts
To set up their attacks, Scattered Canary uses Gmail “dot accounts” to mass-create accounts on each target website. Because Google ignores periods when interpreting Gmail addresses, Scattered Canary has been able to create dozens of accounts on state unemployment websites and the IRS website dedicated to processing CARES Act payments for non-tax filers (freefilefillableforms.com). By using this tactic, Scattered Canary is able to scale their operations more efficiently by directing all communications to a single Gmail account. This removes the need to create and monitor a new email account for every account they create on a website, ultimately making crimes faster and more efficient.
As a result of our analysis, we have identified 259 different variations of a single email address used by Scattered Canary to create accounts on state and federal websites to carry out these fraudulent activities.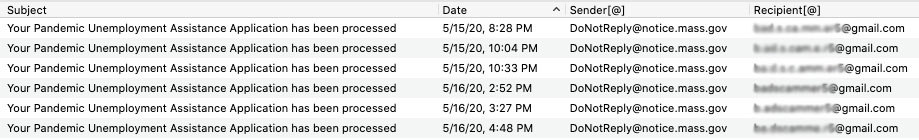
NOTE: Actual email address changed.
Inside Scattered Canary’s Fraudulent Activity
Based on our research, we have observed four recent examples of fraudulent activity that can be attributed to Scattered Canary.
Between April 15 and April 29, Scattered Canary filed at least 82 fraudulent claims for CARES Act Economic Impact Payments, which are meant to provide relief to families as a result of the COVID-19 pandemic. Scattered Canary filed these claims using the website the IRS set up to process claims from individuals who are not required to file tax returns. The only information needed by Scattered Canary to file these claims was an individual’s name, address, date of birth, and social security number. Of the 82 claims Scattered Canary filed, at least 30 of them were accepted by the IRS and presumably paid out.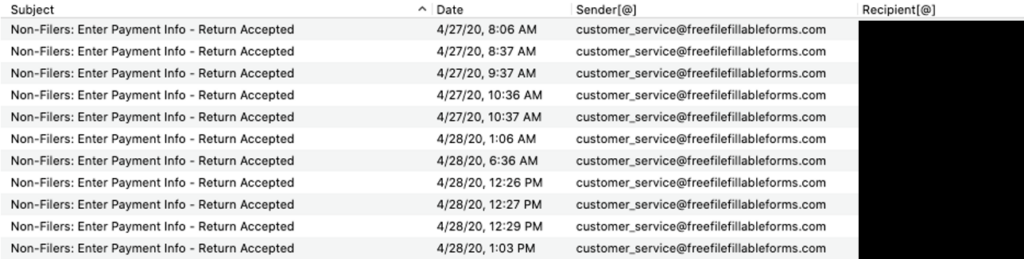
Since April 29, Scattered Canary has filed at least 174 fraudulent claims for unemployment with the state of Washington. This is consistent with previous public reporting of a recent US Secret Service alert mentioning that Washington State has been the primary target of fraudulent unemployment claims. Based on communications sent to Scattered Canary, these claims were eligible to receive up to $790 a week for a total of $20,540 over a maximum of 26 weeks. Additionally, the CARES Act includes $600 in Federal Pandemic Unemployment Compensation each week through July 31. This adds up to a maximum potential loss as a result of these fraudulent claims of $4.7 million.
Between May 15 and May 16, Scattered Canary filed at least 17 fraudulent claims for employment with the state of Massachusetts. Based on our visibility, all of these claims were accepted. While we are not able to see the exact benefit amount for each claim, the maximum weekly benefit is $823 and can last 26 weeks. Adding the $600 pandemic unemployment payment, the maximum potential loss for these claims is nearly $500,000.
Based on our observations of Scattered Canary’s activity, the group seems to be setting their sights on Hawaii as their next target of fraudulent unemployment claims, which has not been previously reported. On the night of May 17, Scattered Canary filed their first two unemployment claims on Hawaii’s Department of Labor and Industrial Relations website. Based on the previous attacks we have observed, Scattered Canary will likely continue filing more fraudulent claims for Hawaiian unemployment in the coming days.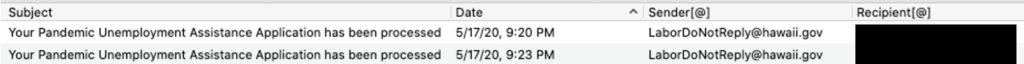
Follow the Money: Where Do These Fraudulent Payments Go?
Our analysis shows that Scattered Canary is using Green Dot prepaid cards to receive the payments from their fraudulent claims. Prepaid cards have previously been a major contributor to facilitating payroll diversion BEC attacks because they can be used to receive direct deposit payments. Green Dot cards are also advertised as being able to receive government benefits, such as unemployment payments, up to four days before they’re due to be paid, making them an attractive tool for groups like Scattered Canary to use in their scams.
We have identified 47 Green Dot accounts that have been used by Scattered Canary to receive fraudulent payments. Notably, each of these accounts has been set up using the name of the individual on behalf of whom the group is filing a fraudulent claim.
No Bar Too Low for Cybercriminals
As we’ve seen across the entire email threat landscape, cybercriminals have been quick to exploit the COVID-19 pandemic. We have seen a more than 3,000% increase in COVID-19-themed phishing attacks since the beginning of February. Phishing attacks targeting a quickly growing remote workforce have increased significantly and BEC actors are evolving their tactics to adapt to stay-at-home orders affecting their targets. So it shouldn’t be a surprise that scammers are also trying to get a piece of the billions of dollars that has flooded the system to try and provide relief to millions of people who have been impacted by the pandemic. And based on what we’ve seen from Scattered Canary’s 10-year history of scamming, they will continue to expand their portfolio of cybercrime to try and find new ways to con individuals, businesses, and governments out of as much money as they can.
An Insider's Look into Scattered Canary
Learn how Scattered Canary grew from a one-man startup into a BEC enterprise.