Today, we’re excited to announce a new technology called Agari Continuous Detection and Response (CDR) that will allow customers to go back in time and find latent threats that are sitting in employee inboxes that could lead to data breaches. As Marty McFly would say, ‘“What do you mean go back in time?”
Let me explain.
Today, Secure Email Gateways (SEGs) and advanced threat protection security controls only check to see whether a message is malicious when it is delivered or forwarded. If on day zero, the attack has nothing that distinguishes it as malicious, then it will get delivered to employee inboxes. However, if there are new sources of threat intelligence such as newly weaponized URLs, zero-day attachments, or new social engineering attack methods that are discovered after the initial delivery of an email, those malicious emails would remain in the user's inbox undetected by existing security controls, posing a threat to the organization as a potential data breach. In most cases, security analysts have to try to find those latent threats before a user clicks, but it can be time-consuming and challenging given the lack of tools to comprehensively and quickly search mail stores.
Cloud Email Protection has a high efficacy rate for advanced email attacks, yet with companies receiving millions of messages per month, there is still a need to constantly search for malicious threats that made it into the inbox if we want to stop all data breaches. To provide a complete solution, Agari continuous detection and response technology dynamically re-scores each messages by applying new threat intelligence to analyze messages that have already been delivered—as if you were going back in time to the original delivery—to discover all the messages in inboxes across your organization and automatically remove them, eliminating potential data breaches.
The underlying technology that makes this possible is the Agari Identity Graph™, which maintains a database of all the characteristics and metadata of all email in current mailboxes in an index that is extremely fast to query. When we receive new threat intelligence, we apply our predictive AI and machine learning technology to root out undiscovered threats 24/7. Because Agari integrates with cloud email systems like Microsoft Office 365 through APIs, we can automatically pull newly discovered malicious messages out of inboxes.
Why can’t Secure Email Gateways and other advanced threat protection systems do this? Most SEGs and APD security controls operate as a hop in the mail flow. So, they get one shot to score a message and then it’s in your employee’s inbox, regardless of what is later discovered about its URLs, attachments, or sender. Email is different than network security. Email threats are stored for years in people’s inboxes and can cause a data breach months after the original attack.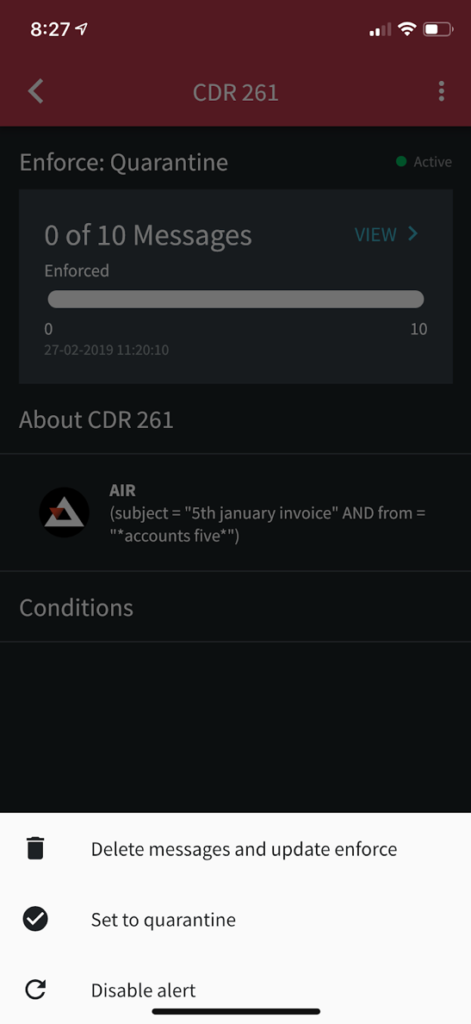
For any of you who have ever been dragged away from your family, significant other, or buddies to deal with an email security incident, you’ll appreciate that we’ve added a continuous detection and response mobile application that will allow you to get push notifications regarding security incidents, triage the incident, and take action to delete or quarantine in seconds—without impacting your work-life balance..
Now that we’ve built this system to continuously monitor inboxes for email threats, we need to feed the machine with world-class threat intelligence, which is where part two of our announcement comes in—the Agari SOC Network.
Great Scott! Agari Introduces Time Travel to Stop Data Breaches
Posted on March 4, 2019