Sophisticated new threat actors, evolving phishing tactics, and a $800,000 business email compromise (BEC) scam in the second half of 2020 all signal big trouble ahead, according to new analysis from the Agari Cyber Intelligence Division (ACID).
As captured in our H1 2021 Email Fraud & Identity Deception Trends Report, successful attacks on Magellan Health, GoDaddy, and the SolarWinds "hack of the decade," one thing has become distressingly clear. Phishing, BEC, and other advanced email threats continue to be one of the most effective attack vectors into organizations. And it's getting worse.
Our report, based in part on intelligence gathered through active defense engagements with BEC actors from July through December 2020, confirms that amid the anxieties and distractions of pandemic-induced work-from-home measures, the success of advanced email attacks has grown far less reliant on technology than on social engineering ploys that easily evade most security controls in use today.
BEC: Well-Organized Threat Actors Raise the Stakes
Throughout the second half of 2020, ACID researchers uncovered a troubling rise in well-funded eastern European crime syndicates piloting inventive new forms of BEC. Indeed, the state-sponsored operatives launching attacks from pirated email accounts in the SolarWinds attack were just a few of the more sophisticated threat actors moving into vendor email compromise (VEC) and other forms of BEC during this period.
But in November, a sudden surge in the amount of money targeted in BEC scams could be tracked back, at least in part, to the resurgence of one particular source—the threat group we've dubbed Cosmic Lynx.
After sewing chaos with COVID 19-themed scams earlier in the year, the group's tactics shifted toward vaccine-related ruses. More alarmingly, the group's emails also started requesting recipients' phone numbers in order to redirect the conversation to phone communications. It's unclear if the request is designed to disarm recipients or if actual phone messages or conversations are now part of the con.
Premium Pretext: The $809,000 'Capital Call' Scam
The second biggest driver behind the late-year increase in the amount sought in BEC scams is a potent new pretext—capital call investment payments.
Generally speaking, capital calls are transactions that occur when an investment or insurance firm seeks a portion of money promised by an investor for a specific investment vehicle.
In emails to targets, BEC actors masquerade as a firm requesting funds to be transferred in accordance to an investment commitment. Because of the nature of such transactions, the payments requested are significantly higher than the average $72,044 sought in wire transfer scams during the last six months of 2020. The average payout targeted in these new capital call cons: $809,000.
Payable on Deceit: Aging Reports Schemes Gain Traction
While hardly a blip for most of last year, our researchers also noted a significant increase in aging report scams.
In these attacks, threat actors impersonate a senior executive in emails requesting a copy of a recent aging accounts receivable report, which typically contain a list of all unpaid invoices and the names and email addresses. With this information in hand, attackers target the company's customers with requests for payment on overdue invoices to a new bank account.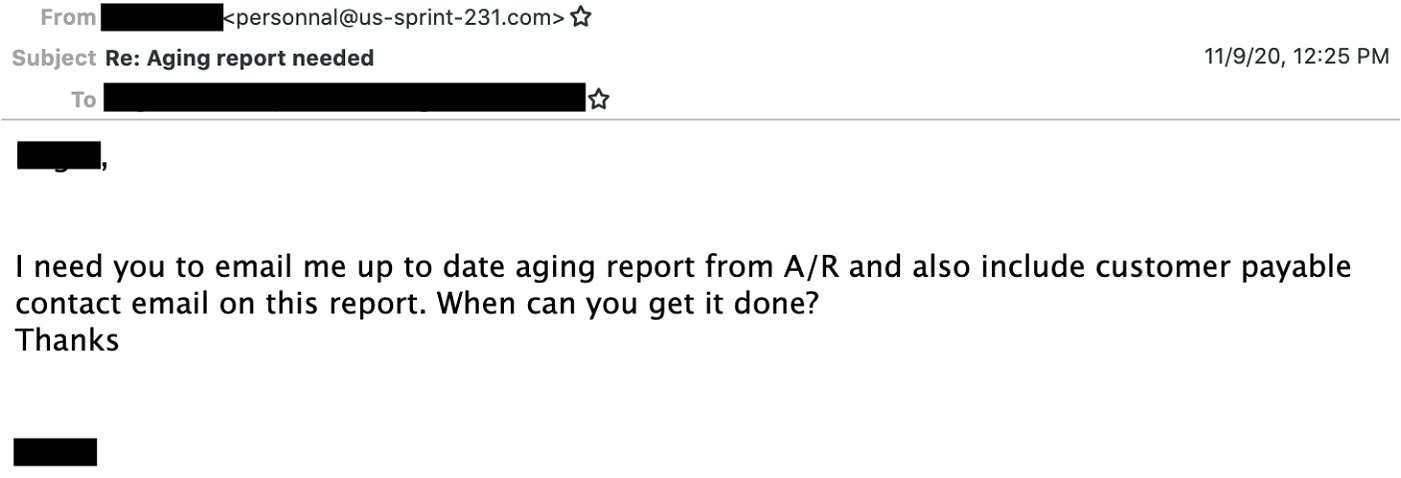
While a large percentage of this increase can be attributed to the BEC group we call Ancient Tortoise, our team identified a growing number coming from actors employing different tactics. Which means the exploitation of aging financial reports may have become its own kind of pandemic, with dangerous new variants coming on the scene.
Gift Card Scams Still Dominate, But Payroll Diversions are Trending
Gift cards remain the top choice for cash-outs in BEC scams, though their popularity slackened during the second half of 2020. In Q3, 71% of all BEC attacks sought gift cards. But in Q4, that figure dropped to 60%.
While wire transfers accounted for 22% of BEC attacks between July and December, ACID researchers noted that payroll diversions are once again on an upward swing. In fact, the number of fraudulent requests to change the employee bank accounts used for direct deposits increased for six straight months to end the year, accounting for 1 in 12 BEC attacks.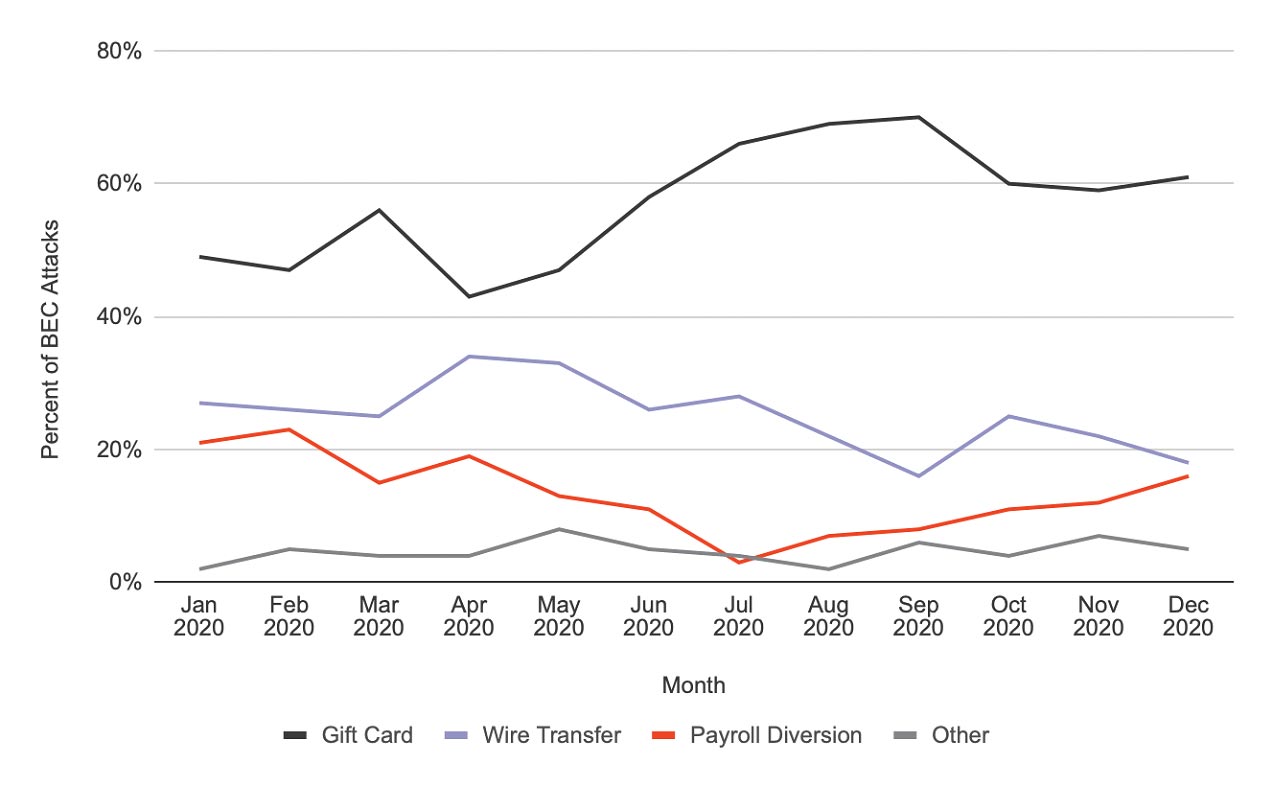
2021 Outlook: More of the Same–Only Worse?
BEC and other advanced email threats have led to nearly $30 billion in business losses over the last four years. But phishing attacks like the kind in the SolarWinds case suggest the price tag could go much higher.
Yet despite the growing risks, it's unclear how many organizations are deploying identity-based phishing defenses capable of blocking advanced email threats—including those leveraging pilfered intel or launched from compromised email accounts.
Given the email threats unearthed during the second half of 2020, let's hope SolarWinds wasn't just a warm-up act for what's to come.
Learn more about the latest trends in phishing, business email compromise and other email threats.