When the Agari Cyber Intelligence Division released our report on London Blue in December, much of the focus was on how cybercriminals use legitimate lead generation services to identify their targets. Research we released today into a different cybergang—one we’ve named Scarlet Widow—shows how Nigerian criminals take a different tactic against more vulnerable institutions.
Rather than focusing on the large enterprises to provide hefty jackpots when compromised, Scarlet Widow preys on school districts, universities, and nonprofits, which the group believes may be softer targets. Since evolving from their historical focus on romance scams, Scarlet Widow has implemented new tactics for generating income from business email compromise attacks.
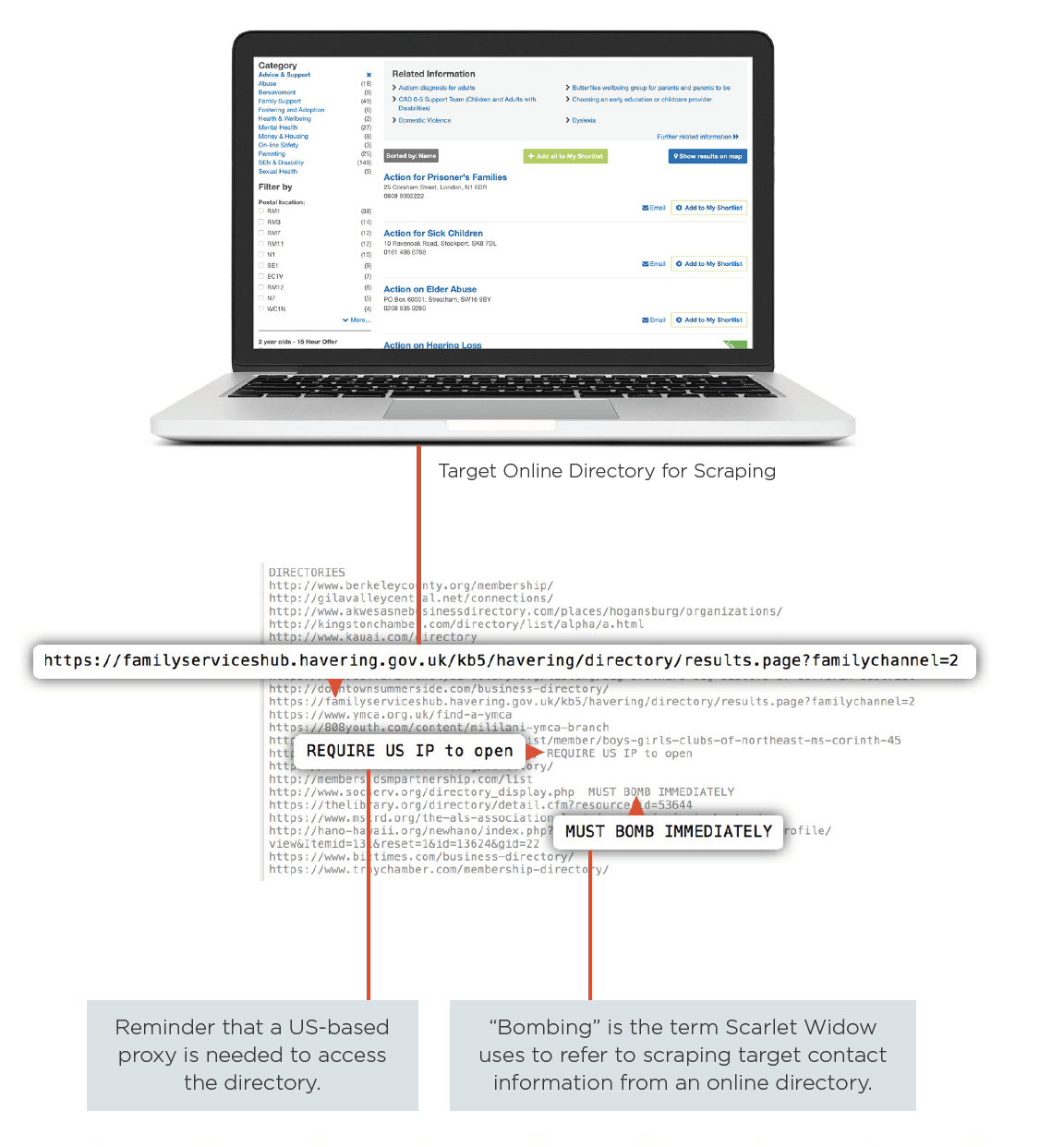
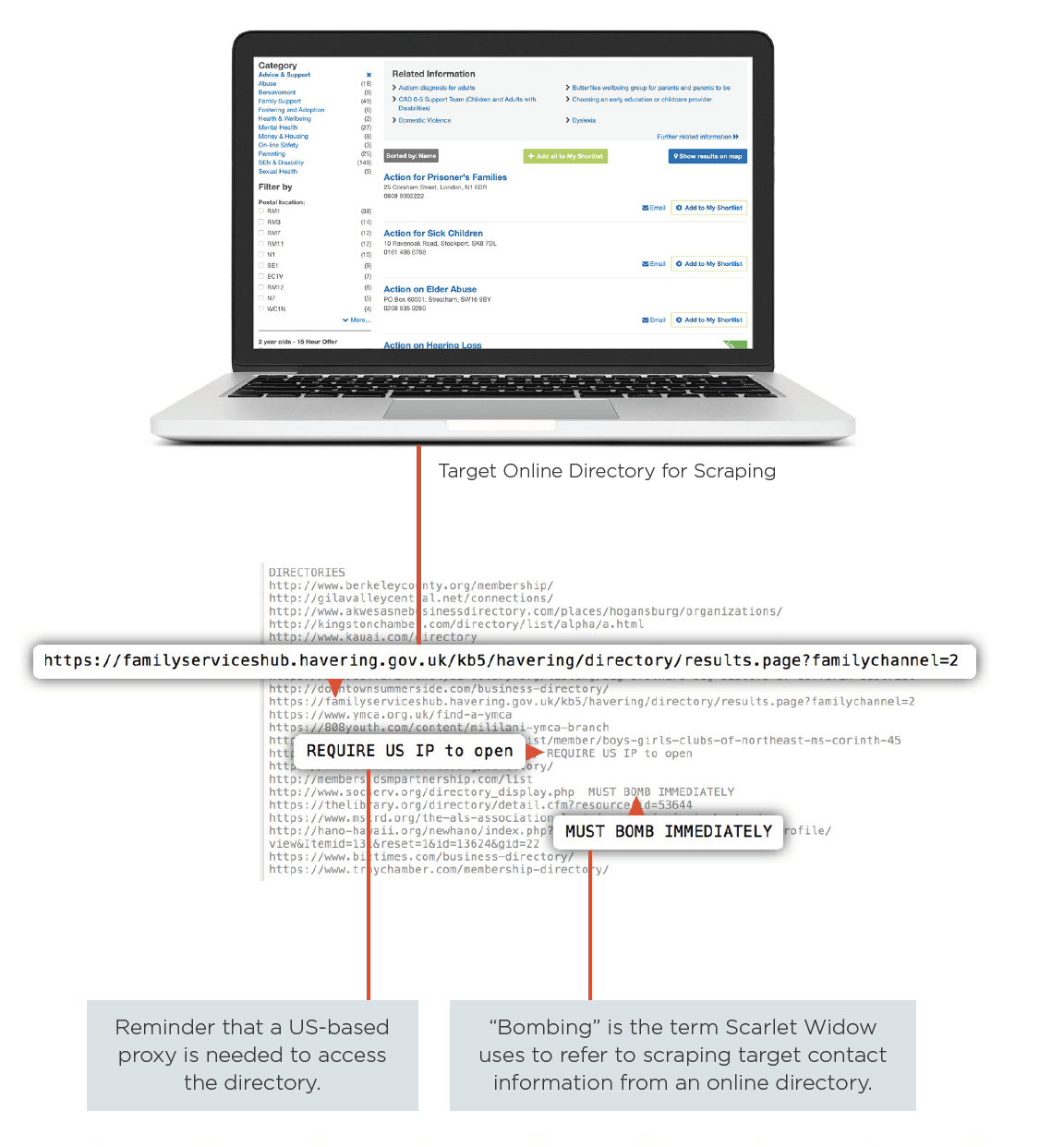
While the group uses commercial tools to identify individual targets within most businesses, when Scarlet Widow goes after nonprofits, the group primarily uses publicly-accessible websites to scrape contact information for employees. Working off a list of identified websites that contain directories of nonprofit organizations, Scarlet Widow uses a web scraper to traverse the online directory and collect email addresses associated with each organization—a process they refer to as “bombing” an online directory.
Since November 2017, Scarlet Widow has gathered targeting information for more than 30,000 individuals associated with more than 13,000 organizations in 12 countries—many of which were gathered through this tactic. Nearly all of the leads collected by Scarlet Widow were for employees located in two countries—with 73% in the United States and 20% in the United Kingdom. Notable targets include the Boy Scouts of America, a West Coast chapter of the United Way, a nationwide anti-hunger charity, a Midwest Archdiocese of the Catholic Church, a well-known annual arts festival, and numerous chapters of the YMCA.
And once Scarlet Widow has successfully targeted an organization posing as an executive or other leader, it is easy for them to launder their money using nontraditional methods. By requesting Apple iTunes or Google Play gift cards rather than wire transfers, the group is able to eliminate associated money mules and safeguard their earnings, far away from bank accounts that could easily get shut down.
Of course, their main objective is not to stockpile gift cards but rather to easily and quickly turn them into cash. Scarlet Widow does this by using two online services: Paxful and Remitano. By first advertising the stolen cards on Paxful, the group can successfully turn them into bitcoin, which they can then trade on Remitano for a specified price. Once the Scarlet Widow actors have exchanged their bitcoin and the buyer’s funds are in their bank account, the process of converting illicit gift cards into cash is complete.
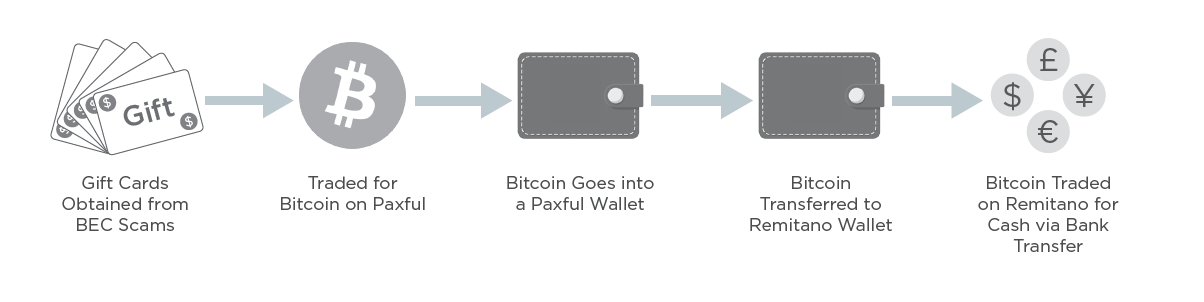
Unfortunately, it’s easy, simple, and fast—meaning that the nonprofits and other organizations scammed out of their money lose it quickly, with no real way to track it down. In one instance, Scarlet Widow attacked an Australian university and converted $1,800 in Apple iTunes gift cards into $700 in bitcoin, laundering it through a Nigerian bank account in less than two and a half hours.
For more information on how Scarlet Widow targets their victims and turns their proceeds into cash, download a full copy of Scarlet Widow: BEC Bitcoin Laundry—Scam, Rinse, Repeat.
Rather than focusing on the large enterprises to provide hefty jackpots when compromised, Scarlet Widow preys on school districts, universities, and nonprofits, which the group believes may be softer targets. Since evolving from their historical focus on romance scams, Scarlet Widow has implemented new tactics for generating income from business email compromise attacks.
While the group uses commercial tools to identify individual targets within most businesses, when Scarlet Widow goes after nonprofits, the group primarily uses publicly-accessible websites to scrape contact information for employees. Working off a list of identified websites that contain directories of nonprofit organizations, Scarlet Widow uses a web scraper to traverse the online directory and collect email addresses associated with each organization—a process they refer to as “bombing” an online directory.
Since November 2017, Scarlet Widow has gathered targeting information for more than 30,000 individuals associated with more than 13,000 organizations in 12 countries—many of which were gathered through this tactic. Nearly all of the leads collected by Scarlet Widow were for employees located in two countries—with 73% in the United States and 20% in the United Kingdom. Notable targets include the Boy Scouts of America, a West Coast chapter of the United Way, a nationwide anti-hunger charity, a Midwest Archdiocese of the Catholic Church, a well-known annual arts festival, and numerous chapters of the YMCA.
And once Scarlet Widow has successfully targeted an organization posing as an executive or other leader, it is easy for them to launder their money using nontraditional methods. By requesting Apple iTunes or Google Play gift cards rather than wire transfers, the group is able to eliminate associated money mules and safeguard their earnings, far away from bank accounts that could easily get shut down.
Of course, their main objective is not to stockpile gift cards but rather to easily and quickly turn them into cash. Scarlet Widow does this by using two online services: Paxful and Remitano. By first advertising the stolen cards on Paxful, the group can successfully turn them into bitcoin, which they can then trade on Remitano for a specified price. Once the Scarlet Widow actors have exchanged their bitcoin and the buyer’s funds are in their bank account, the process of converting illicit gift cards into cash is complete.
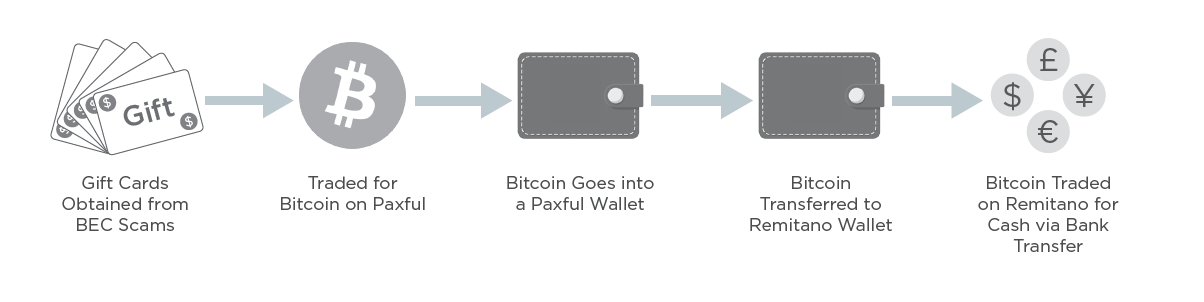
Unfortunately, it’s easy, simple, and fast—meaning that the nonprofits and other organizations scammed out of their money lose it quickly, with no real way to track it down. In one instance, Scarlet Widow attacked an Australian university and converted $1,800 in Apple iTunes gift cards into $700 in bitcoin, laundering it through a Nigerian bank account in less than two and a half hours.
For more information on how Scarlet Widow targets their victims and turns their proceeds into cash, download a full copy of Scarlet Widow: BEC Bitcoin Laundry—Scam, Rinse, Repeat.