Generally defined, cyber threat intelligence is information used to better understand possible digital threats that might target your organization. This data will help identify threats in order to prevent security breaches in the future.
Why Cyber Threat Intelligence is Important
Having a system in place that can produce threat intelligence is critical to staying ahead of digital threats, as well as responding to potential security breaches. From a proactive perspective, threat intelligence can monitor events inside and outside of your network. This helps to identify suspicious activity, and find patterns in cyber attacks that help determine what security features should be implemented next.
From a reactionary standpoint, an intelligence report can be used to review a security incident quickly and provide actionable steps to fix vulnerabilities, mitigate damage, and identify a potential culprit. Cyber intelligence systems are invaluable, especially in organizations where even just a few hours of downtime could have serious consequences for the business.
The 4 Types Of Cyber Threat Intelligence
There are four key types of cyber intelligence that fit into the overall intelligence lifecycle. Each form of intelligence plays a key role in the information gathering process.
Strategic Intelligence
Strategic threat intelligence offers a 30,000 foot view of the threat landscape, and gives decision makers packaged options on how to respond. Strategic intelligence is often the most complete form of intelligence, and is presented as a report or series of options that are less technical in nature. This intelligence often highlights risk factors, groups involved, attack patterns, and other high level insights that are derived from specific requirements and questions.
Tactical Intelligence
Tactical intelligence contains the specific techniques that actors use to carry out a cyber attack. This information can help prepare organizations to defend key assets, bolster security in specific areas, or distribute learning material to help keep staff informed of new threats as they occur.
These intelligence reports contain the tools, vulnerabilities, and specific assets that the attackers are targeting. When delivered quickly, these insights can be used to completely thwart an attack by the time it reaches an organization. Even if an attack does occur, good tactical intelligence will help speed up the remediation and adjust itself to include what was missed.
Technical Intelligence
Technical intelligence is much like tactical intelligence, but relies more on the exact technical execution of the attacks. This type of intelligence often outlines the Indicators of Compromise (IOC), which serve as clues as to exactly what was put at risk, and how a threat gained access.
This detailed information is often used by malware researchers and cyber security professionals to match the attack to known strings of malware, and to forensically document the breach based on the attack characteristic and digital evidence left behind.
Operational Intelligence
Operational intelligence covers detailed, inside knowledge of how a cyber threat conducts its attack. This type of intelligence could contain a list of command and control servers, email servers, aliases, and/or potential targets. It often consists of both technical and non-technical details that, when put together, paint a bigger picture of how an organized cybercrime group functions and carries out attacks.
Having solid operational intelligence helps organizations position themselves to directly counter the specific exploits and vulnerabilities that a particular group utilizes to attack its victims. This can range from blacklisting groups of hostnames and IP addresses, to reinforcing particular areas of a network where attackers are known to try to gain access.
The Cyber Threat Intelligence Lifecycle
Cyber threat intelligence forms a closed loop and consists of six key elements. These elements carry the information to the next part of the process and are all dependent on their previous step. Any type of intelligence can be processed through this system.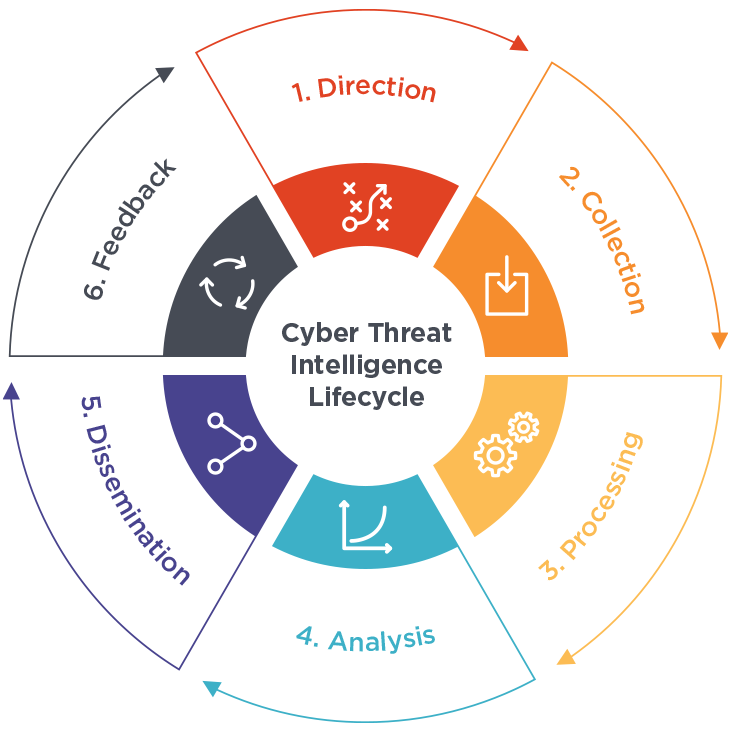
Direction: The first step is to define what information is needed to make informed decisions in the shortest possible time frame. This helps define objectives that are based off of evidence gathered, such as the nature of the attack, devices involved, and what was compromised.
Collection: Data collection can consist of digital and physical evidence depending on the incident. This can include audit logs, IP addresses, CCTV footage, or even physical devices, depending on the nature of the attack. At scale, data collection can exceed terabytes of space, meaning proper planning, storage, and processing will need to be taken into account.
Processing: Raw data is then processed into more organized decipherable forms. This can involve literally decoding information, organizing raw data into groups, or tagging information that fits a specific context or source.
Analysis: A timeline must be established using collected data, and contradictory information must be analyzed further and compared for a clearer understanding of the events as they unfolded. At this stage, patterns and other evidence may emerge, requiring even further analysis. This is often one of the most time consuming stages of the cycle and is almost always led by a human analyst and aided by other tools.
Dissemination: The reports generated from the analysis stage must reach key decision makers so action can be taken.
Feedback: Action is taken based on all the previous steps in the cycle. This could include a retaliation, a new security feature implementation, or could be in the form of adding more data to the cycle for recanalization. Once feedback has been given, the process starts again.
Types Of Cyber Threats
Not all cyber threats are created equal. Here are a few examples of the most common types of attacks experienced today.
Phishing: Phishing is the act of tricking a user into thinking that a message came from a trusted source when in fact it did not. If the recipient believes the message and enters their login details, those credentials are stolen and then used for financial gain or further espionage into a network. Agari Active Defense directly combats and prevents email phishing attacks.
Ransomware: Ransomware has become an increasingly popular tool used among both amateur and professional cybercrime groups. New layers of sophistication makes it difficult to identify before it’s too late. The payload is usually hidden among an attachment in an email, and executed silently in the background, only relieving itself once all of your files have been encrypted. Decryption can cost tens of thousands of dollars for recovery, and even more for larger enterprises or organizations.
Advanced Persistent Threat: APTs are uncommon, but are highly targeted threats that are usually politically or financially motivated. These threats leverage stealth and careful reconnaissance to make their way into a target network to steal, destroy, or spy on an organization. Digital intelligence is key in identifying and repelling these types of attacks. A SOC network can help identify a targeted attack, and dramatically shorten the time frame needed to remove an advanced threat.
Cyber Threat Intelligence Challenges
Proper cyber intelligence goes beyond just a simple firewall or antivirus. It requires continuous detection and response paired with the latest real time threat information. This usually goes well beyond the scope of an internal IT department, and requires the hiring of an analyst, cyber security expert, and response team.
Enterprise level tools for data collection can also be costly to implement and maintain. For internal data collection and analysis, a security information and event management (SIEM) system is usually deployed to collect data from all areas of the organization for aggregation. This centralization is key to analyzing threat data, but can be challenging for most non-technical companies to build on their own. Many companies opt for a threat intelligence integration rather than attempting to build a system on site.
What is ACID?
Others use the work done by ACID, or the Agari Cyber Intelligence Division, which is our counterintelligence research group that partners with businesses to actively defend their organization from cybercrime. Agari utilizes its global threat database combined with strategic alliances to immediately thwart email and social engineering attacks. Check out the full list of threat actor dossiers to stay informed on what it happening in the cybercrime community.
Need protection?
Check out Agari Active Defense for more information on how you can stay protected from cybercrime.