Business email compromise (BEC) scams continue to grow at an unprecedented rate, with more sent by cybercriminals every single day. While they often differ in approach, recent research from the Agari Cyber Intelligence Division (ACID) shows that these text-based phishing attacks possess some commonalities that make them easier to spot.
BEC was a $1.3 billion dollar problem in 2018, and if past trends are any indication, the dollars lost will be even larger this year. Unfortunately, attackers continue to grow more sophisticated in the ways they impersonate brands and individuals, inspiring their targets to act upon their requests before thinking to confirm legitimacy.
To further our understanding of what is changing in the email threat landscape, our researchers identified a few key characteristics common to a growing number of BEC emails over the last three months, which we’ve published in our latest Email Fraud and Identity Deception Trends report.
Gift Cards are King
When BEC attacks first emerged in large numbers approximately five years ago, the primary object was to persuade the target to wire money to a criminal’s bank account under the assumption that they were paying a legitimate vendor invoice. And while this tactic is still in the picture, Accounts Payable and Finance departments have grown aware of it—making it harder to pull off and decreasing revenues.
In response, cybercriminals have changed their tactics. Two other methods—gift cards and payroll diversions—have become the predominant requests from BEC con artists seeking to steal money.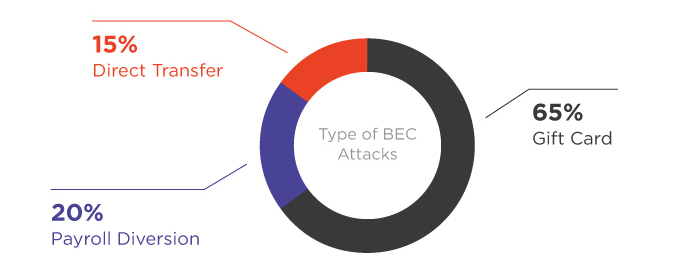
So why gift cards? In comparison to wire transfers, they offer many advantages, the largest being that they are more anonymous, as there a few ways to trace the payment in the same way a bank account can. Making matters easier, they are non-reversible and do not require a money mule or middleman—ensuring that the cybercriminal receives the full payment. And unlike wire transfers, which typically target an employee directly related to the finance department, these emails can target employees in any department, often masquerading as an email requesting gift cards for staff presents or fundraisers.
Still, the approach does come with a downside. While gift cards afford obvious benefits to BEC scammers, one of the biggest drawbacks is that the amount of money an attacker can pilfer per attack is far less with gift cards than with wire transfers. During the past quarter, for instance, the average dollar amount for gift cards requested in BEC scams was just over $1,500.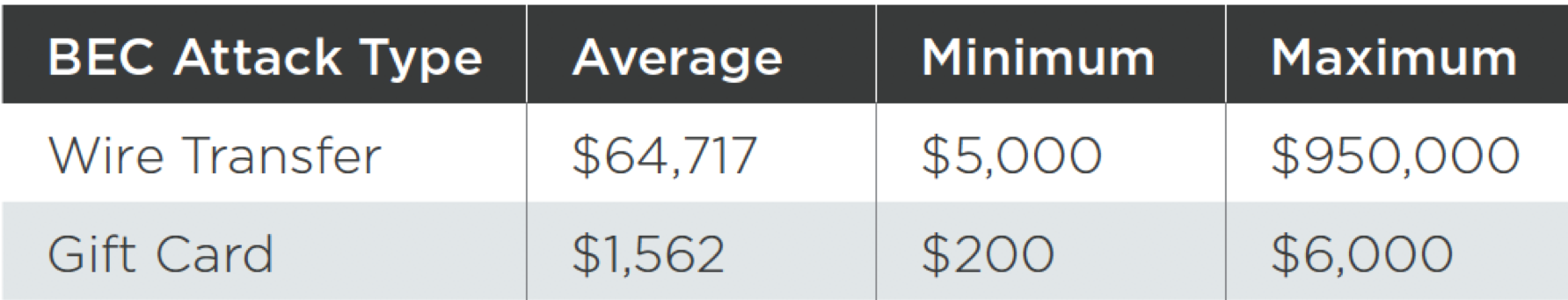
The lesson here? If someone asks for gift cards (or any form of payment), it is always best to check with them for an extra layer of protection. Cybercriminals use Google Play, Apple iTunes, and other types of gift cards to run their scams on a near-daily basis.
Attacks Occur Early
Speaking of a daily basis, recent research shows that BEC scams are sent seven days a week. That said, the vast majority (97%) send attacks on weekdays, perhaps not surprisingly given their targets. What may be surprising to some is just how closely cybercriminals adhere to what are seen as best practices by legitimate email marketers. Despite sometimes conflicting research and variances between industries, a general rule of thumb is that the best day to send an email is Tuesday. During the last quarter, roughly one in every four of all BEC emails arrived on a Tuesday, with the rest tapering off Wednesday through Friday.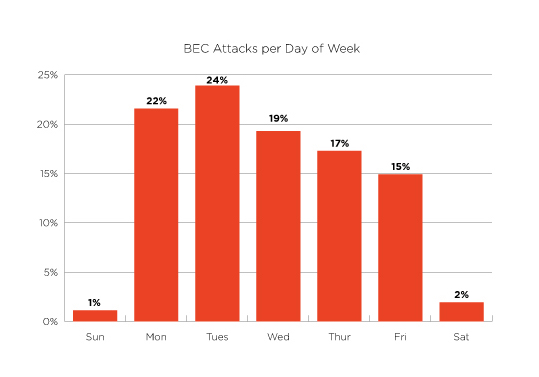
And as far as timing, scammers tend to follow conventional wisdom among many legitimate email marketers which states that it is best to send emails first thing in the morning. Most attacks are sent at the start of the day, with more than half of all BEC attacks distributed between 8 AM and 12 PM. There seems to be a notable preference for 9 AM, presumably aiming to arrive just as someone is sitting down to work in the morning.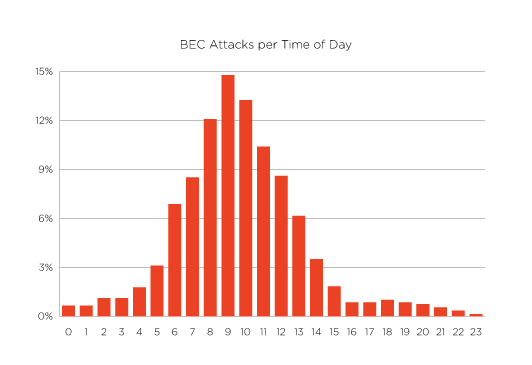
With subject likes like “Request” and “Urgent,” these emails hit at the exact moment that employees are thinking about their commute and their morning coffee, and just when they may be distracted enough to make a critical mistake.
BEC Remains Big Business
As average losses from successful BEC attacks continue to grow, the way organizations respond to this growing threat is of critical importance. Unfortunately, secure email gateways and other legacy email security systems cannot detect these threats as they contain no malicious links or attachments. In contrast, the Agari Identity Graph leverages data science and real-time intelligence from trillions of emails to establish normative, trusted behaviors and signals between email sender and recipient—including devices, message volumes, locations, and more—to spot and neutralize advanced email threats.
Until organizations decide to take steps to protect themselves, BEC scams will continue to reach inboxes. And the eye-popping revenues criminals generate with so little effort will continue to increase by the millions.
Learn more about our recent BEC research in the Email Fraud and Identity Deception Trends report.