The Agari Identity Graph grows smarter every minute of every day in order to protect the world's largest organizations against advanced email attacks.
The Agari Identity Graph is a high-performance graph database of relationships and behavioral patterns between individuals, brands, businesses, services, and domains using hundreds of characteristics to define trusted communications.
The Attack Landscape
Existing Solutions Can't Cut It
There has been a fundamental shift in the email threat landscape as attackers have moved from trying to deceive systems to trying to deceive human beings. These modern attacks leverage identity deception where the attacker sends a message that seems to come from a known identity—an individual, organization, or brand that is often trusted by the recipient.
Traditional email security focusing on inspecting incoming message content and assessing the reputation of a message’s infrastructure of origin can be evaded by identity deception techniques that contain no malicious URLs or content and that weaponize after they hit the inbox.
Agari Detects These Attacks
The technology behind the Agari Identity Graph is focused on detecting the sophisticated identity deception attack using three phases of analysis.
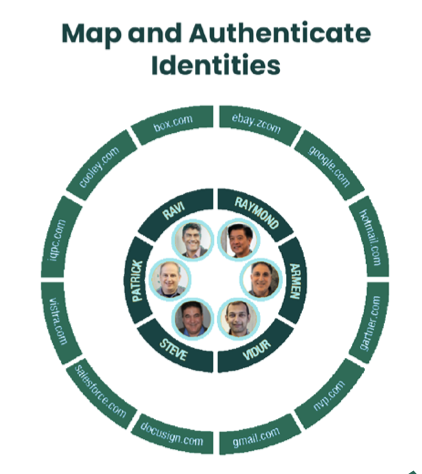
IDENTITY MAPPING
Determines which sender identities the recipient believes is sending the message
BEHAVIORAL ANALYTICS
Analyzes the perceived senders' characteristics for anomalous behavior relative to that identity

TRUST MODELING
Evaluates closeness of relationships; tight relationships (e.g. existing coworkers) have a higher overall risk if they are spoofed

Trusted Email Identity White Paper
This white paper describes an identity-based approach to secure employee inboxes - the foundation of digital communications - using machine learning powered by vast data and email telemetry.