Business email compromise (BEC) actors are exploring alternative cash-out methods for spiriting away the profits from their crimes.
Traditional bank accounts have long been the go-to choice for email scammers seeking to cash out the funds they've pilfered from organizations they victimize. Just since 2016, BEC groups have defrauded businesses out of more than $26 billion worldwide. But over the last several months, countermeasures and changing operating conditions have prompted email fraudsters to seek out new methods to cash out their ill-gotten gains while covering their tracks.
In this post, I'll take a look at some of the top new avenues for cash outs, key drivers behind these new methods, and what your organization can do to protect itself against BEC scams.
BEC: When the Bank is a Cybercriminal Cash-out Machine
For one thing, bank accounts play into the very narrative of these schemes, which can begin with the fraudster posing as a senior executive in emails to a targeted employee asking, "Hey, can you do an urgent wire transfer for me? I need to process a business payment today."
Just in the last four years, dutiful employees seeking to deliver on a senior executive's request have wired more than $26 billion in direct losses to bank accounts controlled by BEC scammers.
This kind of request is standard operating procedure for many businesses, of course. But BEC actors have been exploiting this dynamic to defraud companies out of billions of dollars for years now.
Unfortunately, victim organizations rarely get a glimpse into the true “owner” of these bank accounts, and are often left in the dark about where their money really went. By using an elaborate network of money mules, actors are able to dupe numerous parties into transferring the money from one account to another.
Money Laundering: The Mules of the Trade
In fact, money mules do many things for their handlers, including opening bank accounts, PayPal and other digital currency apps, and in some cases send cash directly to other mules. By putting a layer of obfuscation between the actors and their victims, it makes unraveling the crimes that much more difficult.
Contrary to popular belief, it’s quite difficult to send money directly to Nigeria due to the “scammer” stigma over the years. To help prevent fraud, many organizations have simply opted to not do business in Nigeria, due to the risks associated with fraud.
But at this point, it’s also public knowledge that there are certain criteria and thresholds that have to be met for digital crimes to gain the attention of the FBI and other federal agencies.
In order for email fraudsters to move money around without exceeding these thresholds, the money has to be split, deposited, and withdrawn several times before it finally reaches the final destination.
The problem is that at each step along the way, each participant typically gets some percentage of the funds. For example, if six mules are needed to move money from one bank account to another, there’s a base amount that will be needed to ensure that all six mules get a cut, as well as the amount going to the actor.
BEC: A Rise in Digital Cash-out Methods Testing Smaller Amounts
For some, these costs are merely the price of doing business. For others, this dynamic has been a key driver behind the rising use of gift cards as the primary cash-out method in BEC attacks today.
Indeed, moving money is becoming much more cost effective with new digital technologies, such as Bitcoin. For example, a scammer can ask a victim organization to take pictures of $1,000 worth of gift cards, send them pictures, and the scammer has everything they need to directly convert that $1,000 of gift cards over to something else, like Bitcoin. This is a triple win for the scammers.
First, the scammers are able to attain one degree of separation from the money, which gives them a larger percentage in the end. Second, tracking the digital movement of money from one company to another becomes trapped in layers of subpoenas, increasing the time between identification and possible arrest for the scammers.
And finally, by being able to use smaller amounts, scammers are able to fly under the radar, as smaller caches tend to get less scrutiny than say, a million dollars being wired to another company.
Gift Cards: Not the Only Game in Town
In many cases, a few thousand dollars here or there gets written off by the victim organization, never to see the day of light. Played out across numerous organizations, and pretty soon you're talking real money. Lots of it.
So it's no surprise that in recent months, we have observed BEC actors trying out other types of digital cash-out methods that allow them to diversify their theft, which may point to an eventual pivot away from traditional wire transfers for certain types of BEC attacks.
These alternative cash-out methods include the following and more.
PayPal
BEC actors have been actively testing the waters with PayPal, one of the first companies that people could use to send money from here to there digitally. While PayPal is easy to use in most parts of the world, there are more restrictions on Nigeria-based accounts, so attackers need to use VPN’s and mules to use it as a cash-out method. Based on multiple Active Defense engagements, we know actors have found some level of success using this approach, or else they wouldn't be asking for funds sent to these accounts.
Cash App
While we have only observed a handful of attackers asking for Cash App transfers, attackers are still experimenting with this as a new cash-out method. Cash App is very similar to PayPal and Venmo, except it has one key difference: Bitcoin. By using Cash App, it’s possible to purchase Bitcoin directly from the app. With the nature of Bitcoin, it’s difficult to track—and once funds hit a Bitcoin wallet, it’s incredibly hard to trace, let alone recover, the funds.
Another “good” feature for scammers is the ability to receive a branded cash card that can be used for debit transfers, giving an attacker direct access to funds. If the scammer hasn’t started testing the waters with Bitcoin, they’re able to use these cards to purchase other goods, like ordering merchandise online. In many cases, fraudsters will use reshipping scams to repackage different types of clothing, electronics, and shoes to send to other places around the world.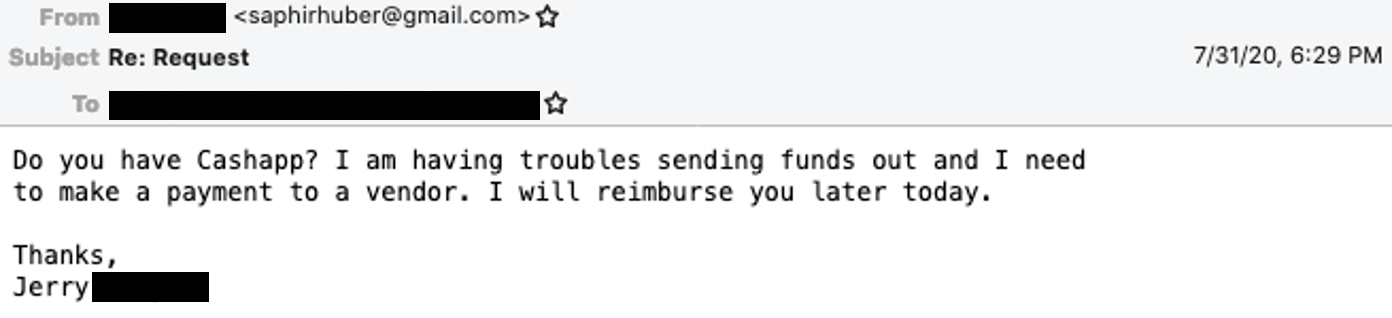
Zelle
With the rise of PayPal and the declining use of hard currency, banks needed more efficient ways to send money from place to place while avoiding the need to know your banking account and routing number. Personally, I can’t recall a single time where I told my friend “Hey, what’s your bank account number? I need to send you some money for pizza.” Zelle is designed to fill that gap, giving customers a quick way to send money back and forth to each other without having to know each other's banking information.
To those unfamiliar with it, Zelle is a digital payments network that partners with multiple financial institutions to enable customers at different banks to send money to one another almost instantly. Just like an ATM card, there are daily limits on how much money you can send. Depending on the length of time you have been with a bank, you can send between $500 and $2,500 per day—and in some cases upwards of $5,000 per day—in just moments.
BEC actors have noticed. If a mule has an account at one of these banks, the scammers are able to use them to receive funds faster than a traditional wire transfer. While there are still limits on how much someone can send at a time, attackers are testing the waters using Zelle as a cash-out method.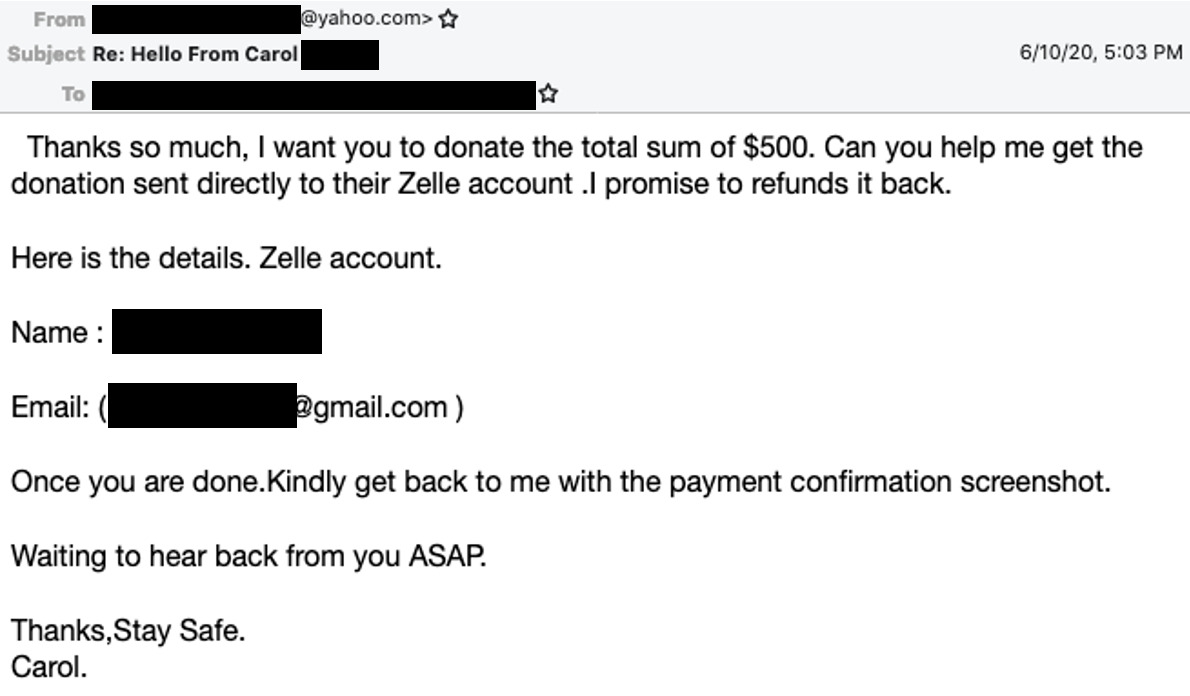
AliPay QR Codes
Recently, we've seen a handful of BEC attacks asking for transfers to AliPay accounts. While AliPay is one of the primary ways to send, receive, and buy goods in China, this is much less popular beyond its borders. Additionally, in order to use most of the functions in AliPay, an account needs to be verified, which requires a phone number and some form of identification (passport, mainland ID, etc.) to pass.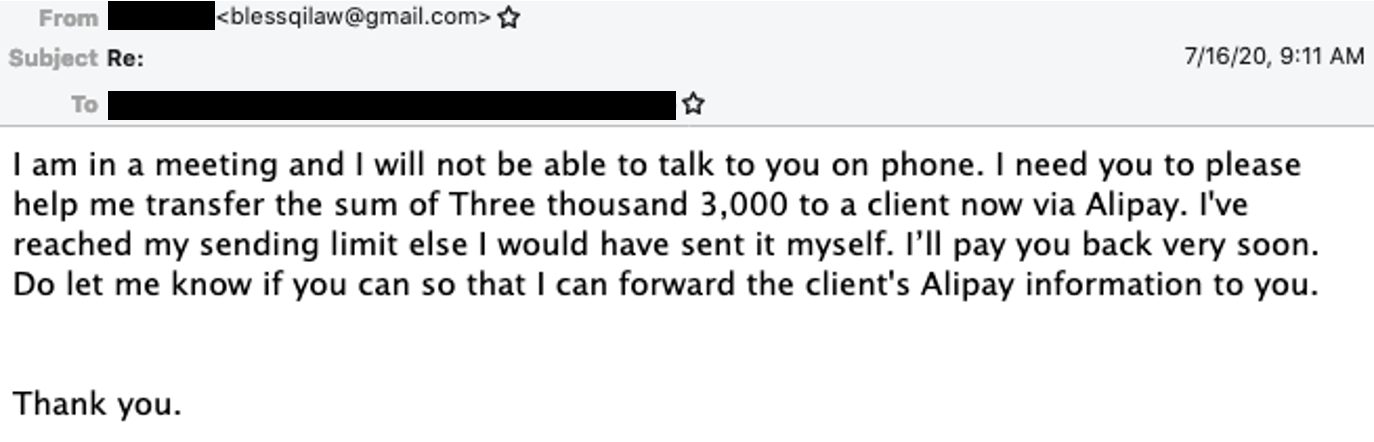
Why Alternative Cash-out Methods?
So why these alternative methods for cashing out proceeds from email scams gaining traction?
Because despite the fact that BEC actors still use bank accounts to move money from one place to another, regulators and processes are quickly catching up—disrupting or preventing a growing number of such transfers.
So far at least, the alternative methods I've talked about in this post are only seen in a minority of BEC attacks. But to diversify their theft models and evade authorities, email scammers are always on the hunt for new and innovative ways to cash out their loot—and it's easy to see why.
Using these and many other cash-out methods, BEC actors are successfully stealing as much as $700 million per month from businesses worldwide.
How to Blunt BEC Attacks
The fact is, it's highly unlikely that your CEO or any high-level executive will ever ask you to initiate a wire transfer, purchase gift cards, or send $200 to a PayPal account in an urgent email message. Yet as many as one-third of all employees will obey these kinds of fraudulent email requests, no questions asked.
To short-circuit such attacks, BEC awareness training, tighter, clearly-defined payment processes, and identity-based phishing defenses can go a long way.