Adoption of Domain-based Message Authentication, Reporting, and Conformance (DMARC) has seen modest growth in recent months, with 6.1 million domains now possessing valid DMARC records, according to our new Q1 2019 Email Fraud & Identity Deception Trends Report.
That's up from 5.3 million in October—a 15% increase in the number of domains protected against email-based "brandjacking" scams that target consumers and businesses by impersonating trusted brands.
Still, while it reflects progress, it only represents a tiny fraction of the 323 million Internet domains surveyed by the Agari Cyber Intelligence Division (ACID) in the largest quarterly study of DMARC adoption rates worldwide. As it happens, there are signs that during the same time period, brands like Yelp, Expedia, Mozilla, and others may have learned firsthand just how dangerous imposters can be.
According to reports, domains associated with these and other brands were allegedly hijacked by cybercriminals and leveraged in a mid-December campaign that included email messages warning about bombs hidden in schools, hospitals, and other public buildings in the United States and Canada. The brand hijacking emails ordered recipients to pay an amount equal to $20,000 in Bitcoin in order to prevent the bombs from activating.
DMARC has proven extremely effective in stopping billions of such email-based impersonation attacks from ever reaching their targets. But as data in the ACID report indicate, most organizations are wide open to such impersonation attacks—including more than half the Fortune 500.
Hijacking Your Brand, Targeting Your Customers
The fact is, brand impersonation scams have surged 11X since 2014, and consumers now lose as much as $172 billion a year through these and other online scams.
At its most essential, DMARC counters the threat by giving brands control over who is allowed to send email on their behalf. It enables email receiver systems to recognize when an email isn't coming from a specific brand's approved domains, and gives the brand the ability to tell the email receiver systems what to do with these unauthenticated email messages.
But there's a catch. Failing to set DMARC enforcement policies results in an easily identifiable vulnerability. Those enforcement settings include monitor-only, instructing the email receiver system to allow the email to be delivered anyway; quarantine; and "p=reject," which blocks the email from ever reaching its target. Failure to implement p=reject results in an easily identifiable vulnerability.
Cybercriminals often spoof domains in order to send large volumes of spam, resulting in damage to the domain name's reputation, blacklisting, and even reputational damage to the brand itself. The effects may first show up in complaints that outgoing emails aren't reaching recipients, often bouncing or being filtered by spam filters.
A Never Ending Blame Game
This is no small matter. Today, email is 40X more effective at acquiring new customers than these other channels. It generates $40 for every $1 spent—by far the highest of any digital medium. And 72% of consumers say they prefer email as their primary mode of communication with brands.
Even when a consumer hasn't been personally defrauded, publicity about attacks bearing your brand identity can mean they'll be hesitant to open the next legitimate email you do send. When your deliverability rates plunge, so can your revenue. And thanks to the outrage overtaking social media, the stigma may have a long-lasting, perhaps even catastrophic, effect on your brand.
Thus the importance of DMARC. As part of our quarterly study, we set out to get a firm read on the state of DMARC adoption across the Fortune 500, FTSE 100, and ASX 100—as well as other large businesses across major verticals—to gauge trends among prominent global organizations across geographies.
The size of our dataset offers an unprecedented view into the number of domains with established DMARC records, as well as how many of those records have been set to the highest enforcement level of "p=reject."
When Half a Solution is None at All
Without a doubt, some of the largest corporations around the world continue to gain traction in terms of email authentication. But almost 85% of the Fortune 500 remain vulnerable to impersonation, as do their customers. Indeed, despite growing 2% last quarter, DMARC adoption remains dangerously low within the Fortune 500, enabling threat actors to exploit the considerable brand equity of even the largest, most well-known and most trusted companies in the United States.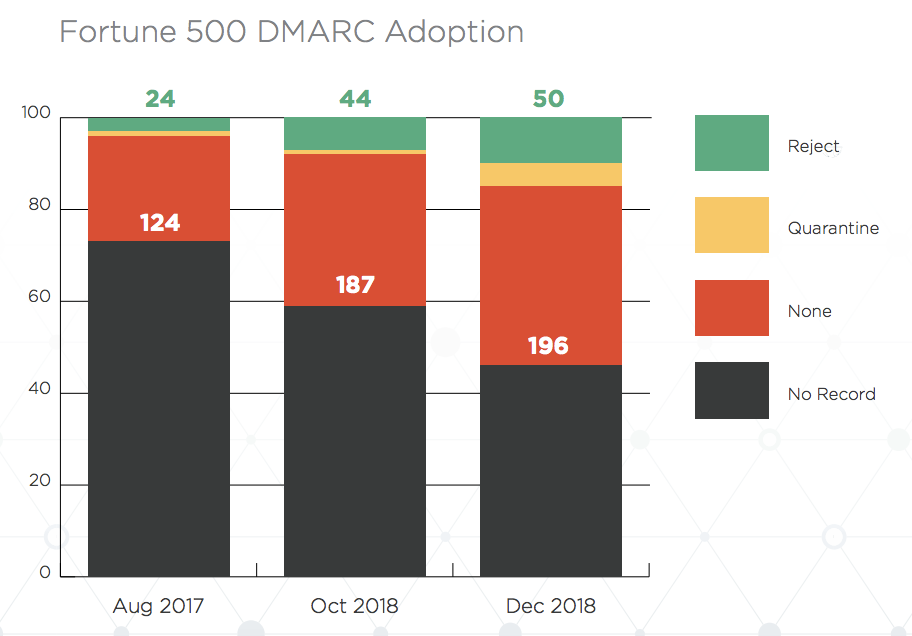
Nearly 50% of the Fortune 500 have yet to publish any DMARC policy at all. Nonetheless, this is a marked improvement from 2017, when more than two-thirds of the Fortune 500 had no DMARC policy. Meanwhile, about 5% have implemented a quarantine policy, about the same as the preceding quarter. And only 1 in 10 has implemented a reject policy to block phishing attempts impersonating their brands.
DMARC: Delivering Serious Returns
According to a study from Forrester Research, organizations using Agari DMARC Protection, for instance, have seen impersonation attempts drop to near zero in a matter of weeks. And by avoiding the kind of negative headlines and brand erosion that result from these scams, organizations have also seen email conversion rates for their own, legitimate email programs climb an average of 10%.
But the bad guys might not be too worried, yet. As it stands now, cybercriminal organizations continue to hunt for more ways to exploit trusted brands in their nefarious schemes. In fact, the same group behind December's bomb scare campaign is believed to be behind recent email-based sextortion cons and may have already misused around 4,000 domains belonging to McDonald's, MIT, Dignity Health and others.
Let's hope it's enough to prompt faster DMARC adoption, along with some pleasant surprises in our next quarterly report.
For more on DMARC adoption across industries and geographies, download a copy of the Q1 2019 Email Fraud & Identity Deception Trends Report.