The first half of 2020 saw 25 additional Fortune 500 companies adopt Domain-based Messaging, Reporting & Conformance (DMARC)—bringing the total to 20% of organizations within the index, according to our H2 2020 Email Fraud and Identity Deception Trends Video .
Which is salutatory, to be sure. But it means 80% of the world's biggest companies haven't adopted the standard email authentication protocol they need to prevent cybercriminals from hijacking their domains for use in email-based brand impersonation attacks targeting their customers and the public.
It also reflects a slower DMARC adoption compared to the 85% growth seen in 2019. And it couldn't be happening at a worse time.
According to the FBI, successful phishing, business email compromise (BEC) scams, and other advanced email attacks were already raking in more than $700 million each month since 2016. Then came COVID-19. From March through June, we documented a 3,000% increase in email attacks specifically designed to exploit the coronavirus pandemic. Brands were impersonated in 66% of these attacks.
Our H2 report includes mid-year analysis from the industry's largest ongoing study of DMARC adoption trends worldwide. It suggests that rising volumes of malicious emails threaten serious reputational and financial damage to the organizations they impersonate.
Brand Impersonation in the Time of Coronavirus
Maybe it's a phony banking account alert, a bogus stimulus payment update, or a fraudulent overdue notice. Whatever the ploy, the emotional stress stemming from the pandemic has only amplified the psychological potency of social engineering tactics used in phishing emails.
Half of the top 10 phishing lures over the last three months were related to the outbreak, according to TechRepublic. And a recent survey from TransUnion finds that 31% of US consumers say they've been hit with pandemic-themed phishing attacks. We've also posted extensively about how imposters posing as suppliers are using COVID-19 as a pretext in attacks designed to defraud entire corporate supply chains.
Make no mistake: The damage done from brand impersonation extends far beyond the immediate victims. Your company may face significant lost business, and even lawsuits. What's more, negative news reports and social media screeds about scams bearing your brand identity can render your legitimate email programs radioactive to recipients, if they're even delivered.
Given the fact that email generates $40 for every $1 spent, having your email-based revenue streams eviscerated could be calamitous at a time when digital channels may be the only way you can connect with homebound recipients.
DMARC is designed to help brands avoid that.
DMARC: Defending Your Brand by Protecting Your Customers
First introduced in 2012, DMARC gives organizations control over who is allowed to send email messages on their behalf.
It does this by enabling email receiver systems to recognize when an email isn't coming from a specific brand's approved email senders, and gives the brand the ability to tell email receiver system what to do with these unauthorized email messages.
Its most aggressive enforcement policy is reject (p=reject), which means email messages that don't pass DMARC authentication will be rejected by a mail server and not delivered to its intended recipient.
So why hasn't every brand adopted DMARC? While deploying DMARC on a single domain is relatively simple, implementing it across an enterprise's total universe of domains—which can span thousands of domains—can get very complicated, very fast.
But according to a study from Forrester Research, DMARC deployments using automated implementation tools like those from Agari have been shown to drive phishing-based brand impersonations to near zero almost instantly, while boosting email program conversion rates as much as 10%.
Today, customers in numerous categories use Agari DMARC Protection™ to manage nearly 230,000 domains with 75%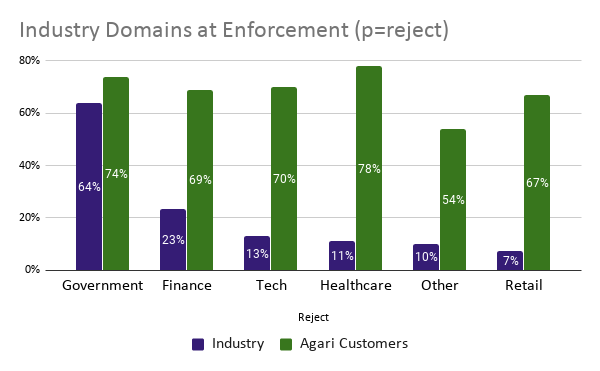
Rising Stakes, Dangerous New Twists
There are a couple of other reasons Fortune 500 companies might want to put DMARC adoption on the front burner right about now.
Earlier this summer, our researchers were the first to document how email threat groups are starting to actively assess a company's level of DMARC adoption before attempting an email-based brand impersonation.
At the same time, the public appears to be getting fed up with brands that don't do everything they can to protect against cybercrimes that end up victimizing customers.
According to an April 2020 survey from Veritas, nearly 65% of consumers say victims should be entitled to financial compensation from such a brand. Another 35% say the CEO should pay a fine, while another 30% think the CEO should be banned from running a company. The list of suggested penalties only gets worse from there.
Don't laugh. If the social upheaval and activism seen over the last few months have taught brands anything, it's that consumer sentiment can change overnight—and nobody wants to be on the wrong side of it.
With email-based brand impersonations on the rise, some companies may decide that deploying DMARC is a whole lot more desirable than explaining to an angry public why they haven't.
To learn more, watch the H2 2020 Email Fraud and Identity Deception Trends Video from the Agari Cyber-Intelligence Division (ACID).